Detecting SeriousSAM CVE-2021-36934 With Splunk
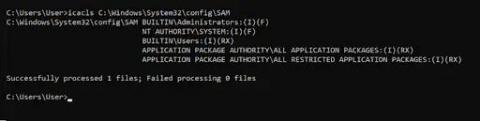
SeriousSAM or CVE-2021-36934 is a Privilege Escalation Vulnerability, which allows overly permissive Access Control Lists (ACLs) that provide low privileged users read access to privileged system files including the Security Accounts Manager (SAM) database. The SAM database stores users' encrypted passwords in a Windows system. According to the Microsoft advisory, this issue affects Windows 10 1809 and above as well as certain versions of Server 2019.