Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest Posts
Integration Exploration: Getting Started with Falcon LogScale and Bucket Storage on AWS S3
If you run CrowdStrike Falcon® LogScale, previously known as Humio, locally or on-premises, one of your first steps is to configure local storage so that LogScale has a persistent data store where it can send logs. If you’re running LogScale as a cluster setup, then you’ll have some data replication as a function of how LogScale manages the data. However, even with that replication, you’ll probably still want something outside of your local infrastructure for resiliency.
Importing Docker Logs with CrowdStrike Falcon LogScale Collector
Docker is the primary tool used for containerizing workloads. If your company wants to build containers with quality, then you’ll need access to your Docker container logs for debugging, validation and optimization. While engineering teams can view container logs through straightforward CLI tools (think docker logs), these tools don’t provide a mechanism for storing or indexing logs over time. A central, remote location for gathering logs from Docker containers is necessary.
9 Ways a CISO Uses CrowdStrike for Identity Threat Protection
Identity isn’t a security problem — it’s the security problem. This was the takeaway from my recent meeting with a local government CISO in the Washington, D.C. area. Tasked with protecting infrastructure, including the fire and police departments, the CISO turned to CrowdStrike a year ago for endpoint and identity protection.
Inside the MITRE ATT&CK Evaluation: How CrowdStrike's Elite Managed Services Operate in the Real World
Following CrowdStrike’s strong performance in the first-ever MITRE ATT&CK® Evaluations for Security Managed Services Providers with 99% detection coverage, we take a deep dive into the testing process and how our elite managed services operate in the real world. We recently announced CrowdStrike achieved 99% detection coverage in the inaugural MITRE ATT&CK Evaluations for Security Managed Services Providers.
Not a SIMulation: CrowdStrike Investigations Reveal Intrusion Campaign Targeting Telco and BPO Companies
CrowdStrike Services reviews a recent, extremely persistent intrusion campaign targeting telecommunications and business process outsourcing (BPO) companies and outlines how organizations can defend and secure their environments.
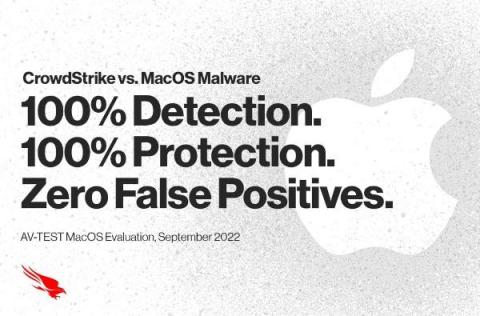
CrowdStrike Falcon Platform Achieves 100% Detection and Protection Against MacOS Malware with Zero False Positives in Latest MacOS AV-TEST
As organizations increasingly face malware attacks that target macOS, detecting and preventing attacks without disruption caused by false positives and false warning messages is increasingly important. That’s why we’re proud to share that the CrowdStrike Falcon® platform once again achieved 100% detection and prevention of macOS malware with ZERO false positives in the latest AV-TEST macOS evaluation.
Spotlight on the Log-Structured Merge (LSM) Tree: One of the Keys Enabling CrowdStrike to Process Trillions of Events per Day
In a previous post, our team shared our Three Best Practices for Building a High-Performance Graph Database. That was written two years ago, when CrowdStrike Threat Graph® was processing billions of events per day and storing a few petabytes of data. Fast forward to today: CrowdStrike Threat Graph now stores over 40 petabytes of data and handles trillions of events per day while routinely serving upward of 70 million requests per second.
CrowdStrike Announces Expanded Service Integrations at AWS re:Invent 2022
At AWS re:Invent 2022, CrowdStrike is announcing expanded service integrations with AWS to provide breach protection across your AWS environment, simplified infrastructure management and security consolidation. Visit us at Booth 109, Nov. 28-Dec. 2 in Las Vegas, to learn more about our comprehensive integrations with AWS.
Make Cloud Defense a Team Sport by Turning DevOps into a Force Multiplier
Enterprises are embracing cloud-native applications in the name of business agility. These applications enable developers to take advantage of the cloud’s scalability and flexibility, allow customers and developers to benefit from the increased velocity of DevOps processes and help businesses quickly react to customer needs and potentially lower their cost of deployment.