Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Featured Posts
How to integrate continuous API fuzzing into the CI/CD?
API security is a growing concern for businesses that offer or consume APIs. APIs, or application programming interfaces, allow different software systems to communicate and exchange data. They allow businesses to build integrations and connect with partners, customers, and other stakeholders. However, as more sensitive data is being shared through APIs, it is essential to ensure that these interfaces are secure and protected from unauthorized access or manipulation. In this blog post, we'll discuss how continuous fuzzing can be a powerful tool to secure APIs and how developers can adopt a "secure by default" approach by integrating continuous fuzzing into SDLC processes.
7 Things You Need To Know About Mobile Threat Defense Services
A modern business needs to secure both physical networks and mobile devices. Here's what you need to know about mobile threat defense services.
OpenAI (ChatGPT) Vulnerability Remediation Concept Work
OpenAI is an artificial intelligence research laboratory that surprised the world with ChatGPT. It was founded in San Francisco in late 2015 by Sam Altman and Elon Musk, and many others. ChatGPT grabbed 1M people's attention in the first six days, and unbelievable AI & Human conversations screenshots are still getting shared. We couldn't resist more to see how OpenAI can help developers and application security teams by sharing remediation guidance. Many application security teams manage millions of security issues on Kondukto, which would eventually save them hundreds of hours.
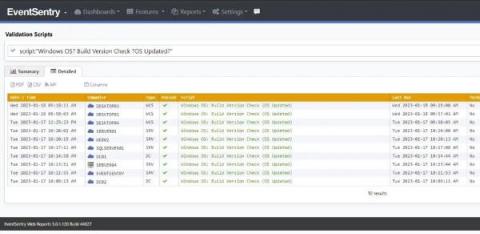
The Life of the Sysadmin: A Patch Tuesday Story
The System Administrator! AKA the Sysadmin. The keeper of the network, computers – well basically all things technology. The one who is hated for imposing complex passwords and other restrictions, but taken for granted when everything works well. They are the first to be called when “facebuuk.com” reports: “domain does not exist”.
6 App Security Tips to Keep Your Application Secure
App security is essential to help deliver the best user experience possible. Read on for more information on keeping your application secure.
Phishing Alert: How to Identify and Avoid Phishing Attacks
Phishing is a type of attack that attempts to steal your personal information, such as your login credentials or credit card details. Cybercriminals use phishing attacks to gain access to your account and steal your data. In this blog post, we will discuss how to identify and avoid phishing attacks. We will also provide tips on how to protect yourself from these types of attacks.
The Payment Card Industry Data Security Standard
As a CIO, you're likely familiar with the Payment Card Industry Data Security Standard (PCI DSS). But what do you know about it? PCI DSS is a set of requirements designed to protect credit and debit card data. It applies to anyone who processes, stores, or transmits payment card information.