Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
July 2021
Build developer trust with faster, accurate AppSec testing from Rapid Scan
Synopsys Rapid Scan helps developers build secure apps with faster, accurate application security testing. The word “rapid” has particular importance when it comes to what developers expect from application security solutions. Anything that slows down development efforts causes friction.
What Will Cybersecurity Look Like Over the Next Five Years?
As a result of the Covid-19 pandemic, organizations in all industries ramped up their digital transformation efforts to make online operations easier for their employees and customers. But with more and more organizations online, the digital attack surface is growing at a record pace. The more applications with vulnerable code, the more opportunities for a cyberattack. In fact, our research found that 76 percent of applications have at least one security vulnerability.
Veracode State of Software Security Vol. 11: Key Findings
What is Cross-Site Scripting?
What is SQL Injection?
Executive Order Update: NIST Establishes a Definition for Critical Software and Outlines Scan Requirements for Software Source Code
On May 12, 2021, President Biden announced an executive order to improve the nation’s cybersecurity. The order, which outlines security initiatives and timelines, calls for the U.S. Department of Commerce’s National Institute of Standards and Technology (NIST) to enhance the security of the software supply chain.
Appknox Webinar: Secure Coding Practices to Prevent Vulnerabilities in SDLC
Continuing on the successful webinar journey, last week Appknox hosted a webinar on "Secure Coding Practices to Prevent Vulnerabilities in SDLC." Focusing on secure coding best practices, our experts busted several myths and misconceptions regarding mobile app security in the webinar and highlighted several client-side misconfigurations which generally go unnoticed by the app developers.
Key Takeaways for Developers From SOSS v11: Open Source Edition
Our latest State of Software Security: Open Source Edition report just dropped, and developers will want to take note of the findings. After studying 13 million scans of over 86,000 repositories, the report sheds light on the state of security around open source libraries – and what you can do to improve it. The key takeaway? Open source libraries are a part of pretty much all software today, enabling developers to work faster and smarter, but they’re not static.
Intelligent Orchestration and Code Dx: Security superheroes
Building security into DevOps has its challenges. Address them with a modern approach to AppSec using Intelligent Orchestration and Code Dx. As a kid, I was fascinated by superheroes like Spider-Man and Superman, and now as an adult I enjoy watching Wonder Woman. There is something about these movies—all the superheroes are unseen and come to the rescue at the right time, and once they have helped, they just disappear without even taking any credit.
Measuring security for cloud native applications
Introducing The Code Dx AppSec Automation Platform | Synopsys
Learn more about Synopsys Software Integrity: https://www.synopsys.com/software-integrity.html
Learning application security by finding and fixing insecure code in OWASP NodeGoat
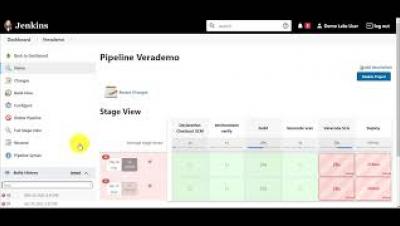
Use the Jenkins Credentials Binding Plugin to Protect Your Veracode Credentials
AppSec Decoded: The state of mobile application security during the pandemic
Watch the AppSec Decoded video to learn about the surprising findings discovered in our mobile application security report.
The Buyer's Guide to Scalable Application Security
Detectify is helping tech organizations bring safer web products to market by providing crowdsourced, cloud-based, continuous web app security. Here’s a buyer’s guide on how you can get scaleable application security in 2021 and beyond. There are so many appsec tools out there with the same features. It’s hard to see value clearly amongst all the noise.