Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
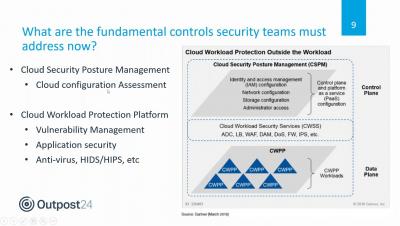
Outpost24 webinar - Cloud security controls best practice
OWASP Top 10 Application Security Risks (With Examples & Recommendations)
OWASP stands for The Open Web Application Security Project. It is a non-profit foundation that works to improve application security for software. Through community-led projects globally, it is a great source for tools, resources, education & training for developers and technologists to secure the web and mobile applications. Read our article to learn more about the OWASP top 10 vulnerabilities with examples.
Detecting Data Exfiltration Via the Use of SNICat
I used to have a cat who loved ice cream. I think I may have given her some as a kitten, and from then on, anytime that she saw someone eating ice cream she would do her best to try and steal some from them. And even if she didn’t really seem to enjoy a particular flavor, she still seemed driven to try and steal that person’s ice cream. Like my cat stealing ice cream, bad guys are constantly trying to target organizations and their data for nefarious purposes.
Autumn 2020 Product Release
Learn about the new product features of our Autumn release including Network Security and DS Agents to help you manage vulnerabilities more effectively and automate security hygiene across the full technology stack with less effort
N-Day Vulnerabilities: How They Threaten Your ICS Systems' Security
In the last quarter of 2019, researchers at ClearSky uncovered an attack operation that they dubbed the “Fox Kitten Campaign.” Iranian actors used this offensive to gain persistent access into the networks of dozens of companies operating in Israel and around the world across the IT, telecommunication, oil and gas, aviation, government and security sectors. These individuals were successful in their efforts because they employed a variety of attack vectors.
Vulnerability scanning vs. Penetration testing: comparing the two security offerings
It’s no secret: the number of security vulnerabilities organizations must contend with is overwhelming. According to a 2019 Risk Based Security report, there were 22,316 newly-discovered vulnerabilities last year. One Patch Tuesday disclosed a record number of 327 vulnerabilities in a single day. Just keeping up is becoming a monumental task. But knowing where and how your organization may be vulnerable is critical to maintaining a healthy security posture.
Understanding and mitigating CVE-2020-8566: Ceph cluster admin credentials leaks in kube-controller-manager log
While auditing the Kubernetes source code, I recently discovered an issue (CVE-2020-8566) in Kubernetes that may cause sensitive data leakage. You would be affected by CVE-2020-8566 if you created a Kubernetes cluster using ceph cluster as storage class, with logging level set to four or above in kube-controller-manager. In that case, your ceph user credentials will be leaked in the cloud-controller-manager‘s log.
NSA list: what you need to know about the top vulnerabilities currently targeted by Chinese hackers Part 2
In our previous blog we covered the first 10 of the NSA vulnerabilities currently targeted by Chinese hackers, here the remaining ones, again demonstrating the predictive power of our risk based vulnerability management tool Farsight
NSA list: what you need to know about the top vulnerabilities currently targeted by Chinese hackers Part 1
This week NSA published a list of the top 25 vulnerabilities that Chinese hackers are actively exploiting, and unsurprisingly the list included some of the most prominent CVEs that we’ve covered in our previous risk based vulnerability management blogs.