Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
OWASP Top 10: Broken Authentication Security Vulnerability Practical Overview
User authentication – the process of ensuring only authorized users have access to controlled data and functionality – is the fundamental cornerstone of web and application security.
A Guide to CSRF
On Sale! Access to your Crown Jewels
Remote Desktop Protocol (RDP) is a communication protocol developed by Microsoft, which provides a user with a graphical interface to connect to another computer over a network connection[1]. Once connected, the remote user will be able to communicate with the machine using their input devices, keyboard and mouse, and to have their screen displaying the output of their actions – as if they were physically connected. Simply put, gaining access to your crown jewels.
What is a vulnerability management program and should your business have one?
The rapid rate of change in attack methods and techniques in today’s cybersecurity landscape has made the keeping of an environment secure increasingly more difficult, causing many to fall into a dangerous state of simply reacting to current threats.
OWASP Top 10: Injection Security Vulnerability Practical Overview
OWASP A1 (Injection) covers diversified injection vulnerabilities and security flaws including SQL and NoSQL injections, OS command injection and LDAP query manipulations.
What's the Difference Between Penetration Testing and Vulnerability Scanning?
Is your network secure from outside attacks? What steps is your organization taking to keep its intellectual property and client data safe? Penetration and vulnerability scanning are two tools that can help identify gaps in your network security. In this article, we’ll look at how you can use these tools to evaluate your companies risk factors and whether penetration testing or vulnerability scanning is the right solution for you.
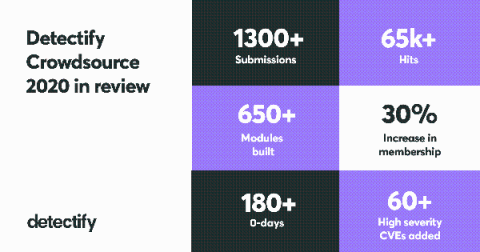
Top 10 Most Critical CVEs Added in 2020
Our global community of hand-picked Detectify Crowdsource ethical hackers are the reason we are able to automate security research so quickly to protect web applications from attack. This past year, we received a record 1300+ submissions from the community including over 180 zero-day vulnerabilities! Every module and security test we build from these hacker-submitted vulnerabilities helps us make the internet more secure.
Monthly Vulnerabilities - December 2020
This bulletin provides an overview of four critical vulnerabilities observed during December 2020, some of which are known to have been actively exploited, and it is recommended that organizations apply all necessary security updates and/or mitigation steps to prevent the exploitation of.
Detect CVE-2020-8554 using Falco
CVE-2020-8554 is a vulnerability that particularly affects multi-tenant Kubernetes clusters. If a potential attacker can create or edit services and pods, then they may be able to intercept traffic from other pods or nodes in the cluster. An attacker that is able to create a ClusterIP service and set the spec.externalIPs field can intercept traffic to that IP. In addition, an attacker that can patch the status of a LoadBalancer service can set the status.loadBalancer.ingress.ip to similar effect.