Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Deceptive 'Vibranced' npm Package Discovered Masquerading as Popular 'Colors' Package
A new malicious package has been detected on the Node Package Manager (npm) repository that poses a significant threat to users who may unknowingly install it. Named ‘Vibranced,’ the package has been carefully crafted to mimic the popular ‘colors’ package, which has over 20 million weekly downloads.
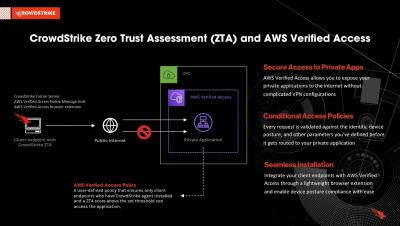
Securing private applications with CrowdStrike and AWS Verified Access
[Head Start] Effective Methods How To Teach Social Engineering To An AI
Remember The Sims? Well Stanford created a small virtual world with 25 ChatGPT-powered "people". The simulation ran for 2 days and showed that AI-powered bots can interact in a very human-like way. They planned a party, coordinated the event, and attended the party within the sim. A summary of it can be found on the Cornell University website. That page also has a download link for a PDF of the entire paper (via Reddit).
Why ChatGPT is a security concern for your organization (even if you don't use it)
ChatGPT may not be used by all organizations and may even be banned. But that doesn't mean you don't have exposure to the security risks it contains. This post looks at why ChatGPT should be part of your threat landscape.
Effective AWS Incident Response: Examples and Recommendations
The use of Amazon Web Services (AWS) in organizations around the world is prolific. The platform accounted for 31% of total cloud infrastructure services spend in Q2 2022, growing by 33% annually. Despite its widespread use, many organizations still fail to consider the nuances of incident response in AWS.
Cloud Identity Security: It Doesn't Taste Like Chicken
There’s a scene in the original “Matrix” movie when Neo is sitting in the grimy kitchen with the rest of the crew and eating gray, runny slop. No matter what new version of gray slop they eat, they always seem to think that it tastes like chicken. When confronted with something new, it’s a natural human trait to relate it back to something we already know.
Ultimate Security Checklist to Launch a Mobile App in Indonesia - iOS & Android
The Association of Southeast Asian Nations (ASEAN) region, including countries such as Singapore, Malaysia, Thailand, and Indonesia, is the fastest-growing digital market in the world. Mobile applications have become increasingly integrated into daily life in terms of financial transactions, eCommerce, healthcare avenues, and service deliveries. That being said, Southeast Asian countries are witnessing a high surge in cybersecurity attacks on mobile applications.
Cloudflare One named in Gartner Magic Quadrant for Security Service Edge
Gartner has recognized Cloudflare in the 2023 “Gartner® Magic Quadrant™ for Security Service Edge (SSE)” report for its ability to execute and completeness of vision. We are excited to share that the Cloudflare Zero Trust solution, part of our Cloudflare One platform, is one of only ten vendors recognized in the report. Of the 10 companies named to this year’s Gartner® Magic Quadrant™ report, Cloudflare is the only new vendor addition.