Meet Jit's AI Agents: The Future of Product Security Work
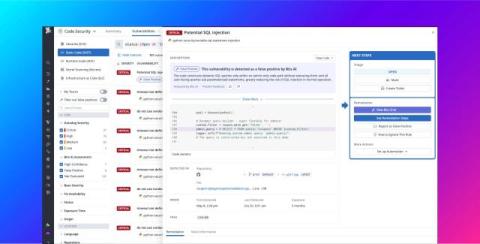
Application security has become too complex — too many scanners, too much noise, and not enough time. Jit’s AI Agents change that. Built on Jit’s Agentic ASPM Platform, these intelligent agents don’t just detect issues — they think like your best AppSec engineer. They correlate findings across systems, validate real attack paths, generate human-in-the-loop fixes, and continuously monitor what actually matters to your business.