Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
The 4 Stages to a Successful Vulnerability Management Program
Have you ever been around someone who is just better at something than you are? Like when you were in school and there was this person who was effortless at doing things correctly? They had great study habits, they arrived on time, they were prepared and confident in the materials that they studied in class, and they were a consistently high performer at every stage?
Security configurations-Part two: 8 imperative security configurations for your arsenal
In part one of this two-part blog series, we discussed seven reasons security configurations are an important part of an organization’s security posture. In this part, we’ll look at eight security configurations that can help with ensuring comprehensive control over the endpoints, avoiding vulnerabilities, deploying security configurations, and automating a number of verticals of endpoint security.
Getting started with adding a new security data source in your Elastic SIEM: Part 1
What I love about our free and open Elastic SIEM is how easy it is to add new data sources. I’ve learned how to do this firsthand, and thought it’d be helpful to share my experience getting started. Last October, I joined Elastic Security when Elastic and Endgame combined forces. Working with our awesome security community, I’ve had the opportunity to add new data sources for our users to complement our growing catalog of integrations.
Why Does Your Business Need Digital Forensic Tools?
While the real world of forensics is much different from your favorite primetime drama, it’s becoming an increasingly important field for the digital sphere. Cybercriminals leave a trace just like real-world offenders, so it’s important to use digital forensic tools that can identify, address, and resolve potentially fraudulent or harmful activities. Keep reading to learn more about digital forensics, and the tools your company needs to stay protected.
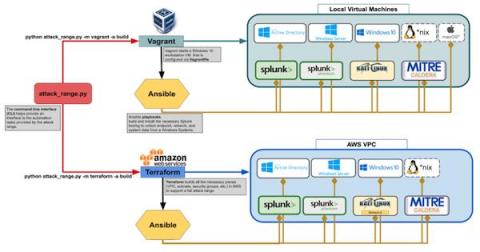
Splunk Attack Range Now With Caldera and Kali Linux
The Splunk Security Research Team has been working on new improvements and additions to the Splunk Attack Range, a tool that allows security researchers and analysts to quickly deploy environments locally and in the cloud in order to replicate attacks based on attack simulation engines. This deployment attempts to replicate environments at scale, including Windows, workstation/server, domain controller, Kali Linux, Splunk server and Splunk Phantom server.
Teramind Named in the Gartner 2020 "How to Choose Between Enterprise DLP and Integrated DLP Approaches" Report
The Report Sheds Light on Data Loss Prevention Challenges and Identifies the Use Cases for Integrated DLP vs. Enterprise DLP Solutions. A recent report published by Gartner titled “How to Choose Between Enterprise DLP and Integrated DLP Approaches” (Gartner subscription required) found that “the data loss prevention market includes products with DLP capabilities integrated in security products or SaaS applications, as well as cohesive enterprise DLP suites.
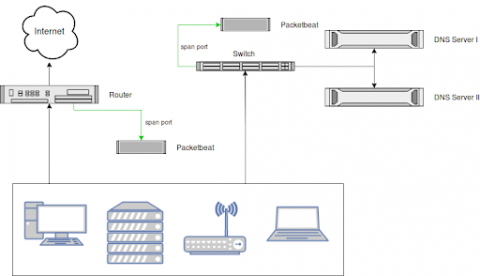
Security Log Monitoring and DNS Request Analysis
Monitoring all DNS requests in your network, including those that were blocked by (e.g., by a firewall) is a great way to increase visibility, enforce compliance and detect threats. A common problem with collecting DNS logs is that DNS server logs are notoriously hard to parse. Also, parsing only the logs of your DNS servers leaves a blind spot when it comes to usage of, or the attempt to use, an external DNS server like Google's 8.8.8.8.
Remote workers making mobile management and security first priority
In recent years, many businesses had already begun planning for a gradual shift towards an increasingly remote workforce, yet fewer had implemented a mobile-first strategy, and some were still formulating strategies. At a gradual pace, IT administrators could handle a small percentage of remote workers and saw the management features of device enrollment programs and network security measures as enough to manage a few remote devices and cyber risks.
May Open Source Security Vulnerabilities Snapshot
May is here, and with it our May’s open source security snapshot, our monthly overview of the new open source security vulnerabilities published in April, to see what’s new in the ever-evolving open source security ecosystem. In order to give you all the low-down on emerging or ongoing trends, our hardworking research team analyzed all of the new open source security vulnerabilities added to the WhiteSource database.