Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Software Supply Chain Security for Open Source Projects
Code to cloud and back to code!
OverWatch Casts a Wide Net for Follina: Hunting Beyond the Proof of Concept
CVE-2022-30190, aka Follina, was published by @nao_sec on Twitter on May 27, 2022 — the start of Memorial Day weekend in the U.S. — highlighting once again the need for round-the-clock cybersecurity coverage. Threat hunting in particular is critical in these instances, as it provides organizations with the surge support needed to combat adversaries and thwart their objectives.
CrowdStrike Uncovers New MacOS Browser Hijacking Campaign
The CrowdStrike Content Research team recently analyzed a MacOS targeted browser hijacking campaign that modifies the user’s browsing experience to deliver ads. Research began with a variant that uses a combination of known techniques to deliver, persist and sideload a Chrome extension. Analysis of the fake Chrome installer uncovered the use of more than 40 unique dropper files to install the extension.
Killnet: Analysis of Attacks from a Prominent Pro-Russian Hacktivist Group
In our new threat briefing report, Forescout’s Vedere Labs leverages a list of IP addresses known to be used by Killnet hacktivists during past attacks to study their TTPs when attacking a series of honeypots we control.
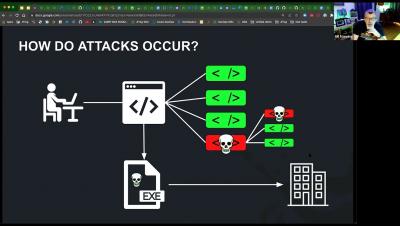
Brute-Force Attacks: How to Defend Against Them
GoodWill Ransomware? Or Just Another Jasmin Variant?
In March 2022, researchers spotted a new ransomware family named GoodWill, with a new method to collect the ransom. Instead of requesting payment through crypto coins like other threats such as Night Sky or Hive, GoodWill requests that its victims help vulnerable people by following a sequence of steps, such as donating clothes, feeding less fortunate children, or providing financial assistance to hospital patients.
Using Rego as a generic policy language
Policies have a vital role in every organization, but can mean a lot of different things depending on the context. For our purposes, a policy refers to the principles or ideas that an organization uses to make decisions. In this post, we’ll discuss Open Policy Agent (OPA) and its rule language, Rego, highlighting how we can use them to write a simple policy for a payroll microservice.
Developing Secure Software With Confidence
Software development and security often have separate challenges and concerns. Developers are worried about pushing software to production in a timely manner. Security teams worry about the security of the code being pushed. Veracode offers a solution that meets the needs of both sides. On Peerspot, where Veracode is ranked number one in application security, users discuss how Veracode enables them to build an advanced application security program.