Introducing Mend Supply Chain Defender Integration with JFrog Artifactory
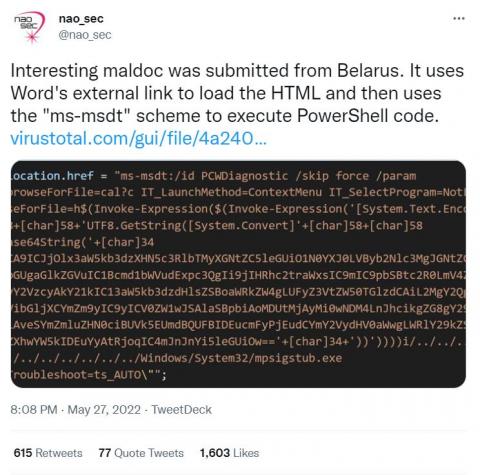
When it comes to understanding the difference between open source software vulnerabilities and malicious threats, it’s helpful to think in terms of passive vs. active threats. Vulnerabilities can be attacked and exploited, but in a vacuum don’t pose a threat. Malicious threats are different —– they involve a threat actor actively planning to attack you.