Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Globee Disruptor Awards names Forward Enterprise 2023 Silver Winner
The Globee Awards for Disruptors recognizes and celebrates organizations and individuals who have significantly contributed to disruptive innovation across various industries. These awards acknowledge the trailblazers who have challenged the status quo, introduced groundbreaking ideas, and transformed traditional practices through their disruptive approaches.
Fortifying data security: 5 features your data store must have
A Broken Industry - 'Changing the narrative of the 'war on cybercrime'
The Future of Transactions: Understanding Secure Subscription Payment Systems
Unravelling the TDIR framework: Conception, evolution, and categorization
Cybersecurity is a mix of both reactive and proactive approaches. In the past, enterprises were often limited to the reactive approach. With compliance and security strategies gaining prominence, the proactive approach is also getting the spotlight. Compared to other industries, cybersecurity is highly dynamic and cybersecurity teams adopt any new technologies that can help them optimize.
19 SEO Ranking Factors That Actually Matter in 2023
7 Critical Considerations A Security Awareness Training Vendor Should Provide
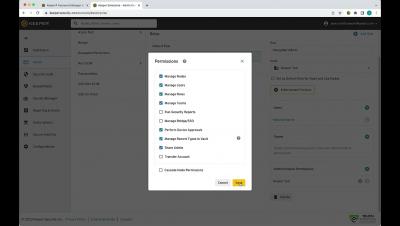
Keeper 101: Record Types
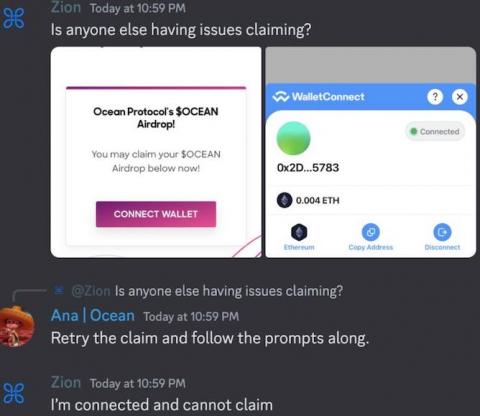
The Bookmark Trap: How Discord Admins Fell Prey to Social Engineering
Brian Krebs wrote: "A number of Discord communities focused on cryptocurrency have been hacked this past month after their administrators were tricked into running malicious Javascript code disguised as a Web browser bookmark. "According to interviews with victims, several of the attacks began with an interview request from someone posing as a reporter for a crypto-focused news outlet online.