Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
4 Things to Know About FISMA
Recently, we discussed the most effective cybersecurity frameworks to reduce the risk of cyber threats. One of the most important systems is the Federal Information Security Management Act (FISMA). This act applies to certain organizations, and is imperative to help protect them against data breaches. Let’s take a look at four things to know about FISMA, from what it is to how to monitor FISMA compliance.
Protegrity: Your Data Privacy Solution
Cloudflare Cache Reserve Walkthrough and Demo
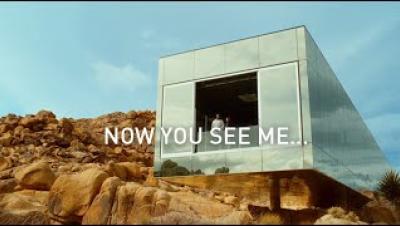
11:11 Systems & Hewlett Packard Enterprise: Rethink Connected
11:11 Systems’ Chief Strategy Officer Dante Orsini recently sat down with our partner Hewlett Packard Enterprise to discuss how we work together to provide leading #DRaaS solutions and deliver on the promise of cyber resiliency.
More information and product details on our website: https://1111systems.com/services/draas-overview/
OpenStack is dead long live OpenStack - The Rise of OpenStack
Launch of Virtru Private Keystore Enables Heightened Privacy and Secure Collaboration in the Cloud
What is CRM Integration? Tools and Examples for Your Business
Going Beyond Network Perimeter Security by Adopting Device Trust
It’s a familiar nightmare you’ve heard of and might even face as a developer or security engineer: alerts firing in all directions warning that your company’s VPN and firewall — that supposedly “safe” defensive perimeter around your infrastructure — has been breached. And the scariest part is that you find out after the fact — after access credentials and customer assets have been stolen.