Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Random but Memorable - Episode 9.7: Delete Message Security Questions
The Financial Industry's Biggest Threat
Losing money to cybercriminals is the financial industry's biggest threat today. Billions of dollars have been lost in 2022 alone due to cyber security incidents. This money is unrecoverable and can be blamed on one thing - poor cybersecurity practices. The money goes straight to the pockets of hackers so they can build bigger and better ways to hack and steal our money.
Industroyer2 and INCONTROLLER: New Findings and How Forescout Protects Against the Most Recent ICS-Specific Malware
In our new threat briefing report, Forescout’s Vedere Labs presents the most detailed public technical analysis of Industroyer2 and INCONTROLLER (also known as PIPEDREAM), the newest examples of ICS-specific malware that were disclosed to the public almost simultaneously, on April 12 and 13. Thankfully, both Industroyer2 and INCONTROLLER were caught before causing physical disruption.
Taking Charge of Application Security
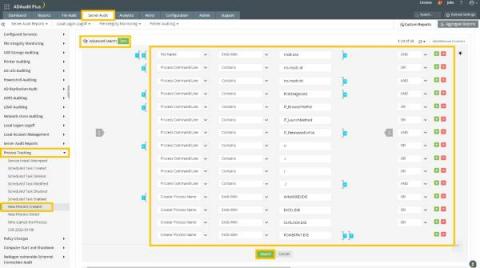
How ADAudit Plus helps you assess your exposure to Follina (CVE-2022-30190)
The recently discovered Windows zero-day vulnerability continues to make news as threat actors across the globe are relentless in their efforts to exploit it. The vulnerability, dubbed Follina, can be exploited when the Microsoft Support Diagnostic Tool (MSDT) is called by a Microsoft Office application using the URL protocol.
DevSecOps deploy and operate processes
In the previous article, we covered the release process and how to secure the parts and components of the process. The deploy and operate processes are where developers, IT, and security meet in a coordinated handoff for sending an application into production.
Themes, Insights, And Leadership Perspectives From The RSA Conference
SecurityScorecard joined U.S. cybersecurity leaders and the cybersecurity community at the 2022 RSA Conference in San Francisco, California from June 5-9. The RSA Conference is one of the world’s leading cybersecurity events, and SecurityScorecard was proud to join our community in-person at San Francisco’s Moscone Center.
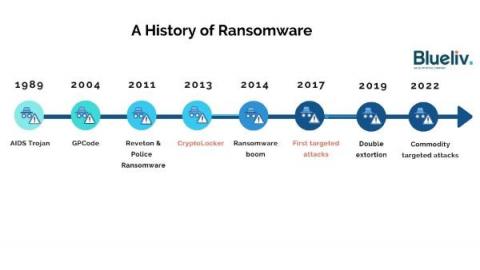
A History of Ransomware
Ransomware is the biggest cyber threat to businesses. First burst onto the scene in 1989, it has evolved significantly over the past few years from widespread attacks to highly targeted ransomware-as-a-service (RaaS) operations affecting organizations of all sizes and sectors. This article takes a look at the evolution of the ransomware ecosystem – what it looks like today, and how it has changed over time.