Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
SOCtails Episode 4 - Respond Fast to Security Incidents with Automated Playbooks
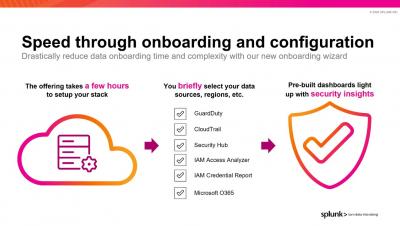
Introducing the World's First Modern Cloud-Based SecOps Platform: Splunk Security Cloud
To say that the past year presented its fair share of cybersecurity challenges to the InfoSec community would be a drastic understatement. The rapid migration to remote work at scale left 80% of CIOs unprepared, and SecOps teams struggled to confront the evolving threat landscape with disparate toolkits and skill sets. Not to mention that as more organizations shifted to hybrid and multi-cloud environments at scale, cloud complexity (and cloud-based threats) skyrocketed.
Splunk SOAR Playbooks: GCP Unusual Service Account Usage
As organizations increase their cloud footprints, it becomes more and more important to implement access control monitoring for as many resources as possible. In previous playbooks, we have shown examples of AWS and Azure account monitoring, but the series would not be complete without also supporting Google Cloud Platform (GCP).
Splunk and Zscaler Utilize Data and Zero Trust to Eradicate Threats
SOARing w/ Splunk Phantom
Super Speed with Phantom Slash Commands
Are you the type of person who loves the command-line? Is tab-complete your friend? Do you move faster on a keyboard than with a mouse? Then Phantom Slash Commands are for you!
Detecting Password Spraying Attacks: Threat Research Release May 2021
The Splunk Threat Research team recently developed a new analytic story to help security operations center (SOC) analysts detect adversaries executing password spraying attacks against Active Directory environments. In this blog, we’ll walk you through this analytic story, demonstrate how we can simulate these attacks using PurpleSharp, collect and analyze the Windows event logs, and highlight a few detections from the May 2021 releases.
Tales of a Principal Threat Intelligence Analyst
At Splunk, we’re constantly on the hunt for new and emerging threats — tirelessly developing detection techniques to zero in on bad actors, while sharing key intelligence around cybercrime activity. But because threat intelligence can relate to so many different things — ranging from spear phishing campaigns to dark web dealings — it can be a challenge to cover and define all the specifics of what (or who) to look out for.