Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
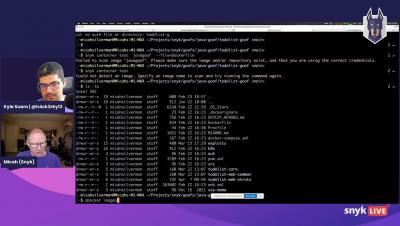
Best practices for managing Java dependencies
Creating Java applications is great, and many resources are available. To speed up development, many folks use frameworks and libraries that do some of the heavy lifting. When looking at modern Java applications, almost all of them contain dependencies from libraries developed by someone else. Dependencies take up about 80 to 90 percent of the binary — so, we should take good care of them when creating a Java project.
Stranger Danger: Your Java Attack Surface Just Got Bigger
Stranger Danger: Your Java Attack Surface Just Got Bigger
CVE-2022-21449 "Psychic Signatures": Analyzing the New Java Crypto Vulnerability
A few days ago, security researcher Neil Madden published a blog post, in which he provided details about a newly disclosed vulnerability in Java, CVE-2022-21449 or “Psychic Signatures”. This security vulnerability originates in an improper implementation of the ECDSA signature verification algorithm, introduced in Java 15.
Just Because You Don't Use Log4j or Spring Beans Doesn't Mean Your Application is Unaffected
By now, you’re probably all aware of the recent Log4j and Spring Framework vulnerabilities. As a recap, the Log4j vulnerability – made public on December 10, 2021 – was the result of an exploitable logging feature that, if successfully exploited, could allow attackers to perform an RCE (Remote Code Execution) and compromise the affected server.
Java Spring vulnerabilities
Several vulnerabilities for Java Spring framework have been disclosed in the last hours and classified as similar as the vulnerability that caused the Log4Shell incident at the end of 2021. However, as of the publishing of this report, the still ongoing disclosures and events on these vulnerabilities suggest they are not as severe as their predecessor.
Two RCE Vulnerabilities Found in Spring Framework
At the end of March 2022, two critical vulnerabilities (CVE-2022-22963 and CVE-2022-22965) were discovered in different components of VMware Spring. Spring is a popular framework focused on facilitating the development of Java applications, including cloud-based apps, eliminating the need for additional code or concerns related to server requirements.
The Next Log4Shell? Spring4Shell Hitting Waves.
How to do password hashing in Java applications the right way!
There are multiple ways to store sensitive passwords. And while having choices can be great, in the context of password storage, picking wrong can be a security nightmare. With that in mind, let’s hash out some of your options 🥁🥁.In this article we’ll discuss how you should hash passwords in your Java applications. While you can apply these principles to any ecosystem, we’ll specifically showcase the best way to handle password hashing in Java.