Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Stranger Danger: Your Java Attack Surface Just Got Bigger
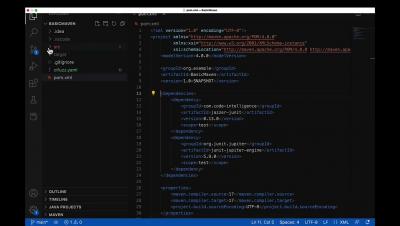
Writing unit tests in Java
Testing is a crucial best practice when developing software. Unit testing is one of the numerous strategies we can use to ensure our code is functional and optimal. As developers, we can code unit tests to check individual components (units) of the application code, such as a specific method. The idea is to write one or more unit tests for each code section and run them every time a change is made to catch defects as soon as they are introduced into the codebase.
How Atlassian used Snyk to solve Log4Shell
Snyk recently launched a multi-day live hack series with AWS, where experts demonstrated exploits in real-time and explained how to defend against those vulnerabilities. This series helped viewers discover new ways to improve security across the application stack for AWS workloads. As part of the series, Micah Silverman (Director of Developer Relations, Snyk) and Chris Walz (Senior Security Engineer, Atlassian) discussed Log4Shell.
Implementing TLS in Java
TLS, or transport layer security, is a protocol used across the globe to encrypt and secure communication over the internet. In this article, we’ll discuss what TLS is, what benefits it provides, and why you need it. Then we’ll walk through implementing TLS in Java.
How to create SBOMs in Java with Maven and Gradle
When building applications in Java, we highly depend on external libraries and frameworks. And each Java package that is imported likely also depends on more libraries. This means that the amount of Java packages included in your application is often not really transparent. As a developer, these nested (transitive) dependencies create the problem that you probably do not know all the libraries you are actually using.
Stranger Danger: Your Java Attack Surface Just Got Bigger
How to use Java DTOs to stay secure
Data Transfer Objects (DTOs) in Java are objects that transport data between subsystems. It is an enterprise design pattern to aggregate data. The main purpose is to reduce the number of system calls needed between the subsystems, reducing the amount of overhead created. In this article, I will explain how DTOs are used in modern Java applications, ways your application can benefit, and how Java DTOs can help you be more secure by preventing accidental data leaks.
What is Java Code Signing Certificate [A Detailed Guide]
Java is a prominent and highly prevalent language in which thousands of software are regularly designed. From social media platforms to popular desktop applications, Java is used to build truly great applications. However, to ensure the safety of Java applications from malware, owners need to obtain a Java code signing certificate. It helps assert the software publisher’s identity to its users and affirm file integrity.