What is an API Gateway?
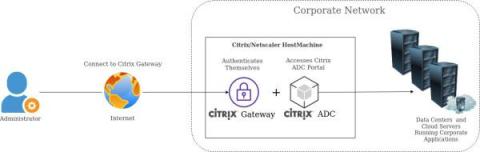
What's a gateway? It is an entry point. Things go in. People, traffic, requests. If you've spent any time with microservices, you may have come across the term "API gateway". While not unique to microservices, the API gateway's popularity has grown in the time since their rise. So what exactly is an API gateway?