Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
%term
Third-Party Risk Assessment Best Practices
Assessing the cybersecurity risk posed by third-party vendors and service providers is time-consuming, operationally complex, and often riddled with errors. You need to keep track of requests you send out, chase up vendors who haven't answered, and ensure that when they do they answer in a timely and accurate manner.
I, CyBOK - An Introduction to the Cyber Security Body of Knowledge Project
The Cyber Security Body of Knowledge project or CyBOK is a collaborative initiative mobilised in 2017 with an aspiration to “codify the foundational and generally recognized knowledge on Cyber Security.” Version 1.0 of the published output of this consultative exercise was quietly released last year and then more publicly launched in January 2020. Yet, this free and information-packed publication does not appear to have captured the attention it perhaps deserves across the wider industry.
Biggest Challenges in Enterprise IT: Data Quality Gap & Data Dispersion
Enterprise data comprising business, operations and assets information, resides in different forms and in different places. While the data is distributed they carry important relationship insights which when leveraged can accelerate and improve decision making to drive the outcomes. This is one of the key challenges that analytics solutions, like AIOps, need to address.
INETCO Insider: Combat the impact of COVID-19 on your payments business
As we head into Q3 of 2020, life is looking quite different for all of us around the world. With many governments beginning to implement plans to ease restrictions, economies are expected to slowly regain their footing. Even as brick and mortar businesses around the world gradually re-open, we will continue to see a trend towards contactless payments, digital banking, online orders and e-commerce.
What is AES Encryption and How it Works?
If your organization offers or needs cyber security solutions, you must have heard of the Advanced Encryption Standard before. In this article, we will take a closer look at AES and how it can be beneficial for your organization. The Advanced Encryption Standard (also known as Rijndael) is one of the most popular global encryption standards, that is why its acronym AES keeps coming up in almost every discussion related to cyber security.
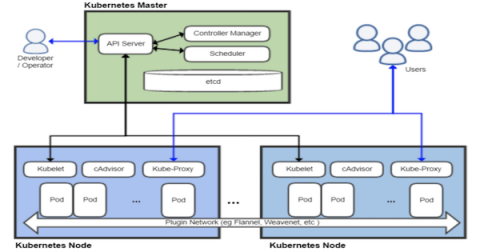
Approaching Kubernetes Security - Detecting Kubernetes Scan with Splunk
The Kubernetes framework has become the leading orchestration platform. Originally developed by Google, Kubernetes is a "platform for automating deployment, scaling, and operations of application containers across clusters of hosts" * . The kubernetes platform is used in all Cloud platform provider vendors as a tool that allows orchestration, automation and provision of applications and specific needs computing clusters and services.
11 Proven Risk Mitigation Strategies
Business is inherently risky. Types of risk abound: financial, legal, regulatory, reputational and more. In the most extreme scenarios, failing to maintain an acceptable level of risk could result in injury or death, as in a factory; or, in the case of critical infrastructure, widespread economic catastrophe.
Stories from the SOC - Office365 Credential Abuse
The most critical element in combating malicious attempts on technology today is visibility. When considering the sheer amount of various cloud, firewall, IDS/IPS, anti-virus, etc. offerings, integrations are a necessity to enable effective security.
What is DNS Spoofing?
DNS spoofing, or DNS cache poisoning, is a cyber attack where false Domain Name System (DNS) information is introduced into a DNS resolver's cache. This causes DNS queries to return an incorrect response, which commonly redirects users from a legitimate website to a malicious website designed to steal sensitive information or install malware.