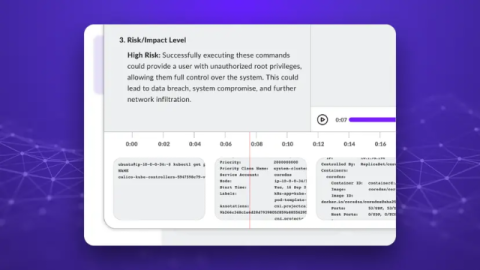
AI Session Recording Summaries for SSH, Kubernetes Exec, and Postgres
Since Teleport 1.0, we have shipped built-in session recording and replay. Nine years later, we are shipping the biggest upgrade yet: AI Session Summaries. Teams using Teleport onboard thousands of engineers (developers, DBAs, Windows users) who run thousands of interactive sessions every day. That easily adds up to 5,000+ hours of recordings per month, which is too much for humans to review proactively.