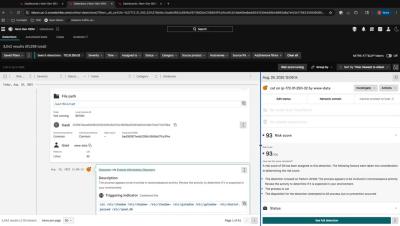
Proactive Lifecycle Management with NQE: EOL, EOS & Compliance Checks
Network teams often risk costly disruptions when aging or unsupported hardware slips under the radar. With Forward Networks’ Network Query Engine (NQE), you can proactively identify devices approaching End‑of‑Sale (EOS) or End‑of‑Life (EOL), plus enforce hardware/software compliance at scale. Get ahead of risks, reduce technical debt, and align your infrastructure with business goals—automatically.