When Seconds Count: Expanding Real-Time Capabilities Across CNAPP
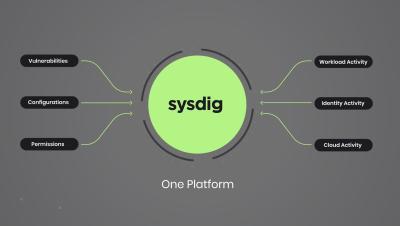
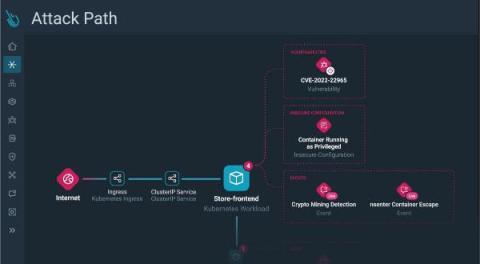
The last few months at Sysdig have seen incredible product velocity as we accelerate our vision to create the leading cloud security platform, also known by the Gartner category Cloud-Native Application Protection Platform (CNAPP). In June, we enhanced our platform with end-to-end detection and response. Today, we are thrilled to unveil a suite of new capabilities powered by runtime insights: Skip ahead to the launch details!