LimaCharlie & Velociraptor Enable the Automation of Deep Forensic Capability
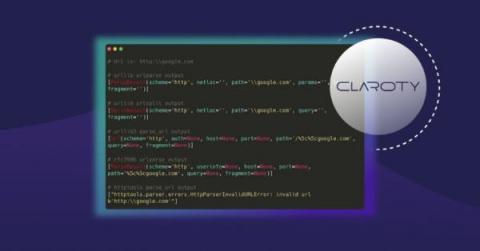
Digital forensics is about answering questions and building timelines. Who did what and when. When something malicious takes place on a computer there is evidence that can be collected and used to reconstruct what exactly happened. Depending on the type of events that need to be reconstructed, the evidence required may be difficult to retrieve. In order to make the lives of DFIR professionals easier, LimaCharlie has integrated the Velociraptor open source endpoint visibility tool.