Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
The Caller is Coming from Inside the House!
SecurityScorecard’s own Ondrej Krehel talks with News 12 in New York about how to protect yourself from what might be the most surreal spam number of all—your own. Most of us are used to getting spam texts: You’ve paid your bill, click this link for a free gift! You’ve won the sweepstakes, click here to redeem! It’s no surprise that nothing good comes from clicking those links.
The Impact of New Federal Banking Regulation
Coffee Talk with SURGe: 2022-APR-19 MS-RPC Vulnerability, Lazarus, Pipedream
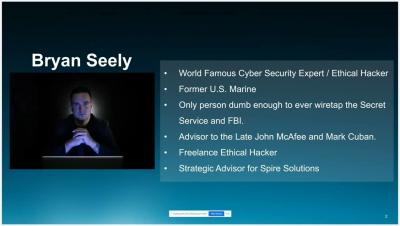
[Thoughtleadership webinar] The emerging cyber threat and attack trends of 2022 with Bryan Seely
Network Evidence For XDR
Wolves or Sheep: How Xray Avoids False Positives in Vulnerabilities Scans
You probably know the story of “the boy who cried ‘Wolf!’” In the ancient fable, villagers tire of a shepherd’s false alarms, and stop paying attention to them. That’s a lesson for software security teams, not just schoolchildren. Raising concerns about threats that turn out to be flimsy or false erodes the trust that binds your department, and even the faith your customers have in you.
The ultimate guide to Python pickle
During application development, we often need to persist complex data (like objects) for use in different runtimes. However, maintaining persistence within complex data structures and objects is far from straightforward. In Python, you can use the built-in pickle library to handle this process. Pickle can serialize a Python object into a flat byte stream (pickling) as well as transform a byte stream back into a Python object (unpickling).
Alternatives to a Corporate VPN
Many businesses use virtual private networks (VPNs) to provide secure remote access to their systems, but this has increasingly become a liability as more people switch to remote work. The greater demands placed on VPNs to offer safe access can expose organizations and employees to security vulnerabilities. In order to better protect their data and systems, organizations may need to seek alternatives to VPNs.
Building communities for developers - an interview with Jeremiah Peschka of Stack Overflow
Michael Fey, VP of Engineering at 1Password, recently interviewed Jeremiah Peschka, staff software developer at Stack Overflow, on our Random But Memorable podcast.