Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Why Are Firewalls Important For Cybersecurity?
This guide has been created to explain the importance of firewalls, whitelisting and blacklisting as part of your IT security protocols in order to protect your system and improve your understanding of this topic as an IT professional. In this resource, we will also cover the key differences between using whitelists and blacklists, as well as why it is important that your security monitoring system includes ways to internally whitelist/blacklist IPs.
Choosing an RDP Client
Controlling your Windows PC remotely can open a world of possibilities; remote work, remote assistance, remote system diagnosis and network troubleshooting are just some of the advantages of using Remote Desktop Protocol or RDP. Developed by Microsoft, RDP allows you to remotely connect to another computer over a network, giving you full access to and control over the computer’s software, data and resources.
Graylog Security
rusted SBOMs delivered with the JFrog Platform and Azure
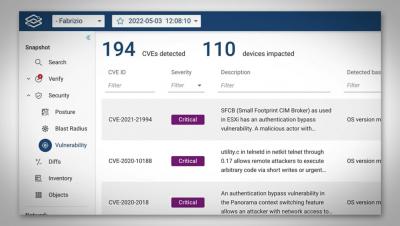
Using Forward's Vulnerability Analysis with Fabrizio Maccioni
A day In The life of a Fashion Products Company CISO - Vikas Yadav
JSON Basics: Building Blocks for Workflow Automation
Automation workflows add a lot of value to an organization’s day-to-day operations. At a minimum, they streamline the execution of complex, multi-step processes, thereby allowing people to focus on higher-value tasks. On top of that, automation workflows can provide valuable insights through the metrics that they gather – including the number of requests, the date and time they were requested, the time it took to complete each request, who made the request, and much more.
What you need to know about PCI 4.0: Requirements 10, 11 and 12
As we continue our review of the 12 Requirements of PCI DSS version 4.0, one has to stop and consider, is it possible to have a favorite section of a standard? After all, most guidance documents, as well as regulations are seen as tedious distractions from the importance of getting the job done. However, depending on a person’s position and function in an organization, it is possible to “geek out” on some of the information in these official papers.
Easily remediate the CVEs most likely to harm you using Forward Enhanced Device Vulnerability Analysis
Headline grabbing vulnerabilities, like SolarWinds and Log4Shell, target management software and end hosts, but if you search for “most exploited vulnerabilities” on Google, you will quickly learn that some of them directly target network and security devices as well as server load balancers. These are the 3 most exploited CVEs in the last couple of years: Would you be surprised to learn that network device operating systems can be vulnerable to security flaws like any other software?