BlackGuard stealer extends its capabilities in new variant
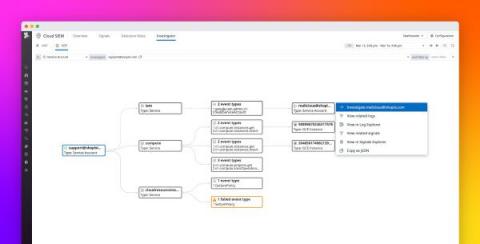
AT&T Alien Labs researchers have discovered a new variant of BlackGuard stealer in the wild, infecting using spear phishing attacks. The malware evolved since its previous variant and now arrives with new capabilities.