Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
How to Detect and Mitigate the 3CXDesktopApp Supply Chain Attack
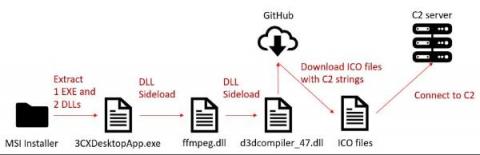
On March 29, researchers from two security companies identified an active campaign originating from a modified version of a legitimate, signed application: 3CXDesktopApp, a popular voice and video conferencing software. 3CXDesktopApp is developed by 3CX, a business communications software company. According to its website, 3CX has 600,000 client organizations and 12 million daily users.
Demystifying Elastic Security for Cloud and its capabilities
3 Ways AI Transforms Security
Security AI usage has surged, and enterprises are reaping the benefits. In its 2022 Cost of a Data Breach Report, IBM found that organizations deploying security AI and automation incurred $3.05 million less on average in breach costs – the biggest cost saver found in the study. According to the study, organizations using security AI and automation detected and contained breaches faster. However, while leveraging AI clearly makes a difference, organizations must implement the right architecture.
Tame the CVE Beast using a Digital Twin
There are never enough hours in the day to do everything. I think we all have a to-do list that is at least twice as long as the time available to complete it. To cope, we prioritize what’s “on fire” or what has the most potential to immediately cause damage if it’s not taken care of. Often the things we “should” focus on fall to the wayside as they are outshined by what we must do immediately.
Majestic Care's Middletown Location Experienced a Serious Data Breach
Majestic Care is a nursing home company that has more than 20 locations throughout Indiana. The organization serves elderly patients all over the state and manages a great deal of medical and financial information as a result. That's why it's so upsetting to hear that one of the company's 20 locations was hit by a cyber attack that resulted in the loss of data. If you or one of your loved ones uses the Middletown location, you may have lost important data and could be at risk.
Securing your Digital Life: MFA, Password Managers and Risk
In security, there are always tensions; the balancing act between security, convenience, and functionality. While these three, often competing interests cause many people to become frustrated, there are some simple steps that can ease the security struggle.
Tripwire and Fortra: Helping Secure IT and OT Environments Better than Ever
When I was younger, you could add a second processor to a computer, but it didn’t double the workload it handled. Natural inefficiencies meant that 1+1 was approximately 1.5 or maybe 1.75 times the workload. Today, multiprocessing and multithreading is so common that even the Windows calculator takes advantage of the benefits. So, when I look at the recent acquisition of Tripwire by Fortra, how do I calculate the result of 1 + 1?
OFAC and Vendor Management: What You Need to Know
Are you aware of the risks involved in doing business with parties sanctioned by the Office of Financial Assets Control (OFAC)? How does this impact your vendor management? OFAC stands for Office of Foreign Assets Control within the Treasury Department. As part of the U.S. government measure to enforce anti-money laundering/counter terrorism financing regulations, OFAC oversees economic and trade sanctions. These sanctions are against countries, individuals, or outfits engaged in disreputable actions.
What Is IoT Device Management? Definition, Key Features and Benefits
IoT Device Management (IDM) is a software platform that helps businesses manage their IoT devices, from identifying and tracking assets to automating operations. IDM features a wide range of features to help businesses manage their IoT devices. IoT device management platforms allow you to remotely control, monitor and update your entire fleet of IoT devices at scale.