The Vendor Tiering Series: Mapping Tiers to Inherent Risk
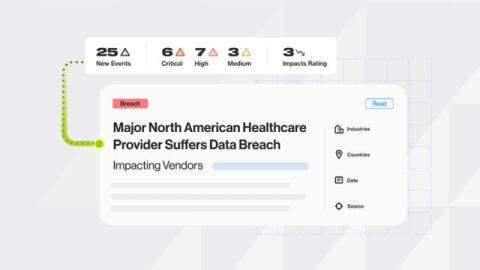
Cybersecurity doesn’t really have quiet days. Usually, it’s just long stretches of constant noise before realizing you’ve been blindsided. That blindside is a flat list of unprioritized vendors. Without a way to filter what matters when a team needs to mitigate the fallout of a crisis, a vendor inventory like this becomes a compliance-only activity that offers a false sense of security.