Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Aikido Security raises Euro5m to offer a seamless security solution to growing SaaS businesses
Less than half of UK businesses have strong visibility into security risks facing their organisation
Elevate Trust and Transparency with Vanta Trust Center
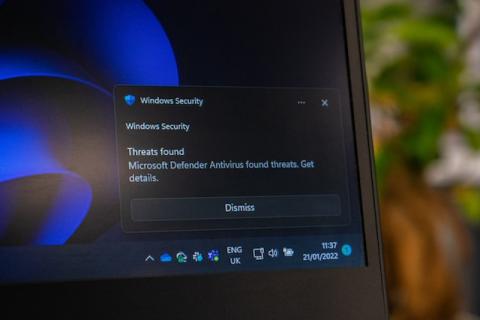
Privacy and Security on Windows: VPN Features Unveiled
Insider Risk Management for Your Cloud Infrastructure: Why Do You Need an IRM Program?
Detecting account compromise with UEBA detection packages
Weather Forecast: Money Is Going to Rain from the Cloud
Since the start of Bitcoin in 2009, the popularity and prevalence of cryptocurrencies has exploded, resulting in a net worth of over $1 trillion that continues to grow. Cryptocurrency—held in virtual wallets—is obtained by users who purchase coins on a cryptocurrency exchange, receive coins as payment from someone else, or “mine” coins virtually themselves.
DDoS attacks have increased by 40% over the last six months
Distributed denial-of-service (DDoS) attacks have been around for a long time. However, the sophistication and scale of these threats has grown in recent years. Cybercriminals are employing amplification techniques that exploit vulnerabilities in misconfigured services or network protocols to increase the traffic they can generate and maximize the impact of their attacks.
Announcing Ruby - your new Generative AI companion for Data Security
Say hello to Ruby, your new Generative AI companion for the Rubrik Security Cloud. Ruby is designed to simplify and automate cyber detection and recovery, something that IT and Security teams struggle with as cyber incidents are getting wildly frequent and the attacks are evolving quickly. A study by Rubrik Zero Labs revealed that 99% of IT and Security leaders were made aware of at least one incident, on average of once per week, in 2022.