Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Multi-Factor Authentication (MFA) Bypass Through Man-in-the-Middle Phishing Attacks
One of the key tools at the center of social engineering attacks against organizations is phishing. According to the Anti-Phishing Working Group’s latest report, the number of unique phishing websites detected in December 2021 was 316,747, where they have detected between 68,000 and 94,000 attacks per month in early 2020, meaning that phishing attacks have more than tripled from 2020 to 2021.
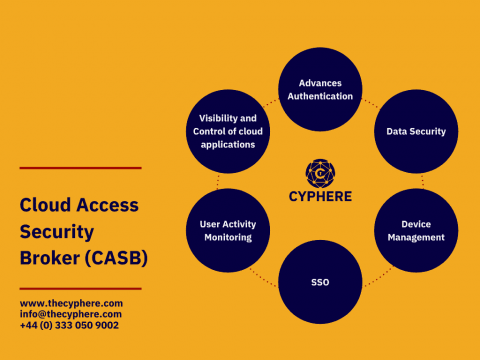
What is a Cloud Access Security Broker (CASB security)?
Cloud access control is a critical part of cloud security strategy. Without granular controls in place, unauthorized users could gain access to your data or even take down your entire cloud infrastructure. Solutions such as Cloud access broker solution (CASB) help you enforce access controls by acting as a layer separating users and cloud service providers.
US Government warns of new malware attacks on ICS/SCADA systems
Agencies of the US Government have issued a joint warning that hackers have revealed their capability to gain full system access to industrial control systems that might help enemy states sabotage critical infrastructure.
Trustwave Security Colony Vendor Assessment: Know Your Vulnerabilities Before Others Do
This is the second installment in Trustwave’s in-depth tour of our Security Colony platform. For a broad overview of what Security Colony offers please read 5 Ways CISOs Can Leverage the Power of Trustwave Security Colony. Self-evaluation in any area, much less cybersecurity, can be challenging. Is my performance at work strong and consistent? Am I being friendly to my neighbors?
Co-edit Microsoft 365 Files With Egnyte for Better Collaboration
With Egnyte, you can now co-edit files in Microsoft Word, PowerPoint, and Excel—either online or via your desktop. And because these files are stored in Egnyte, you get additional security and governance capabilities so you can collaborate confidently, without having to worry about exposing sensitive data. This post explains how.
Sysdig achieves AWS DevSecOps specialization within AWS DevOps Competency
Sysdig is pleased to announce that it has achieved Amazon Web Services (AWS) DevOps Competency for development, security, and operations (DevSecOps). This designation highlights the value provided by the Sysdig platform to AWS customers to achieve their DevSecOps goals. As a key partner for the ecosystem, Sysdig collaborates closely with AWS and its customers to enhance the protection of cloud infrastructure and applications against continuously evolving security threats.
How to plan & manage your hardening project Infographic
Why you need both SIEM and SOAR to improve SOC efficiencies and increase effectiveness
Secure Redis Authentication Using Teleport Database Access
As part of our Teleport 9 release, we added support for three more databases: Redis, MariaDB, and Microsoft SQL Server. In this post we’ll cover the steps needed to protect your Redis instance using Teleport Database Access. Teleport Database Access allows you to easily secure your databases using security best practices such as identity-based SSO, short-lived certificates for engineers or service accounts, multi-factor authentication, RBAC, and audit of all access and queries.