How To Work with Amazon S3 on Amazon Linux
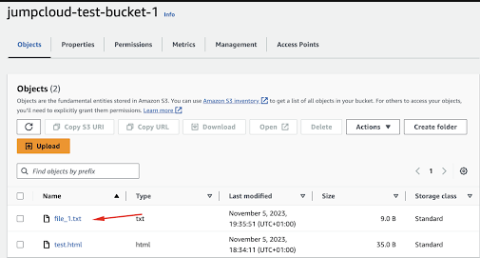
Jump to Tutorial Amazon Simple Storage Service (Amazon S3) is a scalable, high-speed, web-based cloud storage service designed for online backup and archiving of data and applications on Amazon Web Services (AWS). It is designed to make web-scale computing easier for developers and allows you to store and retrieve any amount of data, at any time, from anywhere on the web. Amazon Linux, on the other hand, is a Linux server operating system from AWS, which is engineered for high performance and stability.