Asset Visibility and Behavior: The Keys to Segmentation Success
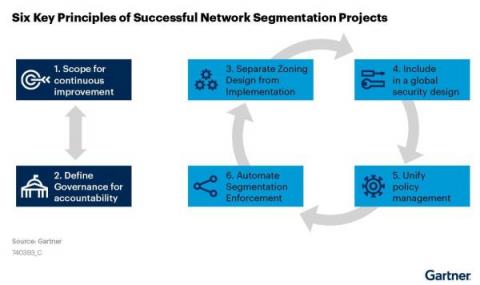
Recently, Gartner® refreshed one of its foundational cybersecurity research, “The 6 Principles of Successful Network Segmentation Strategies.”1 The principles covered in the research are tried and true. Segmenting networks to improve security and performance is nothing new to security teams, yet the same challenges persist year after year.