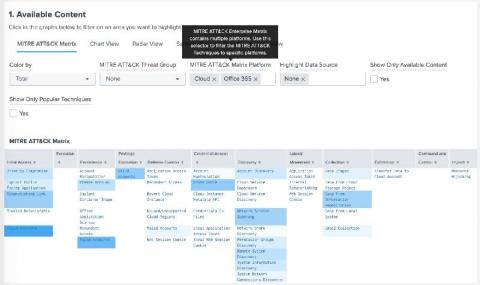
How MISP Enables the Cybersecurity Community to Collaborate During the Pandemic
As if the pandemic itself weren’t causing enough pain and suffering in the world, cybercriminals are busy developing and deploying COVID-19-related malware to try and take advantage of unsuspecting victims. Fortunately, one of the world’s leading technology companies, Microsoft, is taking action to help people avoid becoming victims of these scams.