Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
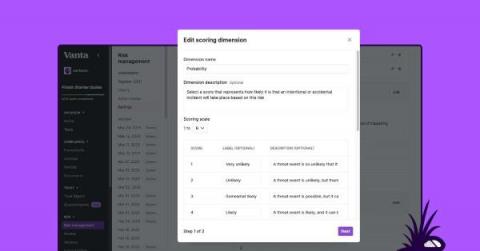
Improve your risk posture: Introducing Risk Management customization
Today we’re excited to announce Risk Management customization, a collection of new capabilities in our platform that enhance the existing Risk Management solution and give you more flexibility to enable custom risk management scoring and prioritization. Currently in beta, Risk Management customization will be generally available in the coming months.
Public Sector Software Security Two Years After Cybersecurity Executive Order
When the Public Sector wins, we all win. Rooting for the security of Public Sector software is something that comes naturally to Veracode. Federal agencies are tackling an incredibly difficult job, and the road to success is meaningful to us all – regardless of our sector or industry. The push for software security came strongly via specific requirements in the Executive Order on Improving the Nation’s Cybersecurity in 2021.
Extending visibility through our new ICS/OT collection
Increasingly, security teams are tasked with identifying, understanding, and managing risk around devices that may live outside the traditional IT umbrella. Operational Technology (OT) refers to computing systems that are used to manage and process operational functions as opposed to administrative operations, with Industrial Control Systems (ICS) being a major segment of that OT sector.
Maximizing Security: How Biometric Integration Supports Large Banks and Organizations
In an era of increasingly sophisticated cyber threats and identity fraud, ensuring robust security measures has become paramount for large banks and organizations. As traditional authentication methods prove vulnerable, biometric integration emerges as a game-changing solution.
Harnessing Biometrics and Face Recognition for Robust Security in Complex Organizational Systems
Biometrics revolutionizes the authentication landscape by leveraging unique biological characteristics, such as fingerprints, iris patterns, and facial features. Unlike traditional methods, biometrics provides a highly reliable and secure means of identity verification. Among these modalities, face recognition emerges as a convenient and non-intrusive approach that ensures robust security while enhancing user experience.
10 Out Of 10 SecOps Pros Agree: You Can't Secure What You Can't See
Network complexity is at an all-time high. Between legacy technology, hybrid-multi-cloud environments, and networks cobbled together by mergers and acquisitions, it’s impossible for people to keep track of the network, its topology, and behavior. The idea of trying to trace a path through a multi-cloud network seems akin to being asked to pull a rabbit out of your hat.
Xalient named one of the FEBE Growth 100 fastest growing founder-led private companies
Secure network transformation specialist, Xalient proudly announced today that it is part of the FEBE Growth 100 list for the second consecutive year. FEBE champion’s the fastest-growing, founder-led private companies headquartered in the UK. The Growth 100 highlights founders that are driving their companies to deliver significant sales, revenue and profit, against a backdrop of unprecedented economic challenges.
The Power of Generative AI and Lessons Learned from Zenith Live 2023
It was great to be both a sponsor and a participant at Zenith Live in Las Vegas last week. Attended by security architects, CIOs and CTOs, the caliber of presentations was exceptionally high. We heard from Zscaler CEO, Jay Chaudhry, about many industry-redefining innovations around AI-enabled security, data-driven business intelligence insights, and product enhancements which promise to further strengthen the Zscaler platform.
Honeypot Recon: MSSQL Server - Database Threat Overview '22/'23
In a constantly connected world, protecting sensitive data in what are often complex database structures requires staying up to date with cyber criminals’ malicious attack techniques, and infection methods. This research is an extension of another project which involves monitoring attacks carried out on database servers worldwide. Understanding how these bots work can keep your digital world safe and secure.