Managing Storage Access: Secure Cloud-native Development Series
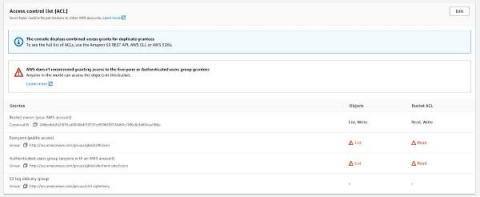
Build secure cloud-native applications by avoiding the top five security pitfalls we lay out in our Secure Cloud-native Development Series. This blog is the third part of the series, and it will teach you how to secure cloud storage and handle access controls on S3 buckets. Each cloud provider has managed storage services that your organization is already probably utilizing.