Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Convince Your Boss You Need These Managed IT Security Services
Considering managed it security services? It is more important than ever to have a resilient security posture. Hackers are constantly looking for ways to exploit weaknesses in systems, and even a small data breach can have devastating consequences.
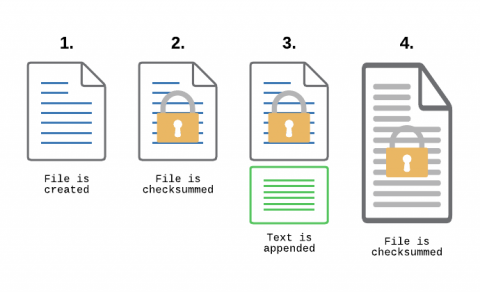
Monitoring Transaction Log Files for PCI compliance
File Integrity Monitoring, aka as FIM, is a must-have feature for anyone in charge of security. With FIM, one can detect when a critical file, such as a file that belongs to the Operating System, or a key configuration file, is changed. In most cases, configuring FIM is straightforward: If the file changes then generate an alert.
Security Basics: Incident Response and Automation
Incident response is one of the most challenging tasks that IT teams face. It's challenging not just because it typically involves many stakeholders and moving pieces, but also because teams usually face pressure to respond as quickly as possible. That's why investing in incident response automation is a wise choice. Although it may not be possible to automate every aspect of every incident response workflow, being able to automate at least the major elements of incident response will yield incident management processes that are faster, more reliable, and more consistent.Keep reading to learn about the components of incident response and which incident response activities to start automating.
Why Composable Analytics Matter for Multi-Cloud AIOps
Zero Trust is not a shortcut to security
Ransomware 2022: Facts and Statistics
In 2021, Ransomware Attacks cost businesses an estimated $11.5 billion. But that's just the beginning of the story. What about all the other consequences of ransomware attacks? How do they affect businesses? In this blog post, we'll take a look at some of the most important ransomware facts and statistics for 2021. We'll also discuss what businesses can do to protect themselves from these devastating attacks.
How a Cyber Security Maturity Model Protects Your Business
Cybercrime is costing businesses around the world billions of dollars each year. And, as we become increasingly reliant on technology, the threat of cyber attacks only grows. To protect your business from these threats, you need a cyber security maturity model in place.