Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Gravity: Running Cloud Applications in Remote, Restricted and Regulated Environments.
How to SSH Properly
There’s no denying that SSH is the de facto tool for *nix server administration. It’s far from perfect, but it was designed with security in mind and there’s been a huge amount of tooling written over the years to make it easier to use. In addition, many popular products and just about every server deployment system integrates with SSH somehow.
Work from home better with secure and reliable enterprise service
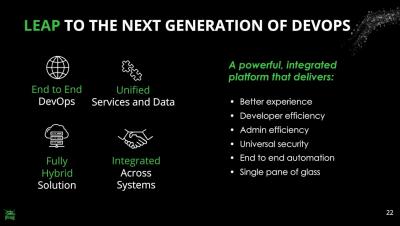
DevSecOps Best Practices with JFrog Platform
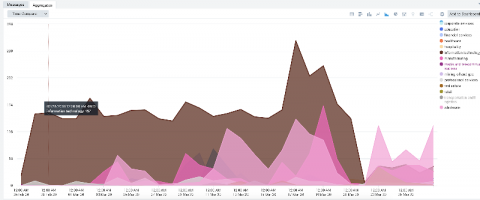
Application Security Testing Trends
According to a recent Forrester report, the application security market will exceed $7 billion by 2023, with security scanning tools leading. Clearly, organizations increasingly understand that securing their application layer is important, and they are prepared to invest substantial resources in protecting it.
What COVID-19 teaches us about Micro-segmentation and Run-time Cloud Workload Protection
March 2020, the Coronavirus is pretty much everywhere. As I am writing these lines, the number of cases worldwide is 341,334 and 192 different countries have experienced infections.The world is fighting this epidemic and travel limitations are widely used in order to control the spread of the disease. While some say these restrictions are critical, others claim it to be ineffective and redundant. I am not an epidemiologist and will leave that analysis to the experts.
Top trends from the CNCF survey & what it means for enterprises
The results are in! The Cloud Native Computing Foundation (CNCF) seventh annual survey was recently released, showing that cloud-native technologies have become mainstream, and that deployments are maturing and increasing in size. This cloud-native shift means developers can more easily build complex applications, and organizations can deploy and manage these applications more quickly and with more automation than ever before. Don’t have time to read the whole thing? We’re here for you.
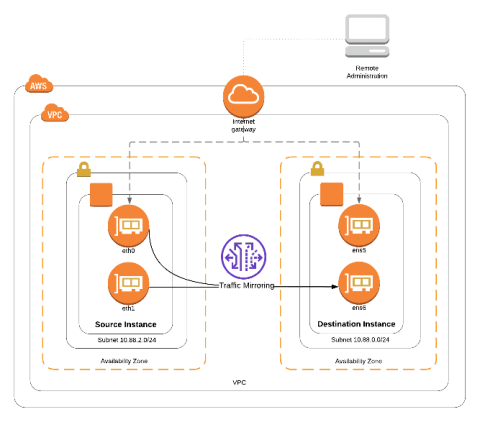
Amazon VPC Traffic Mirroring
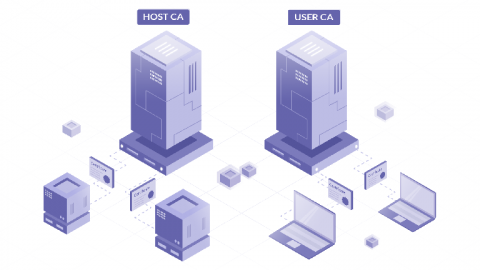
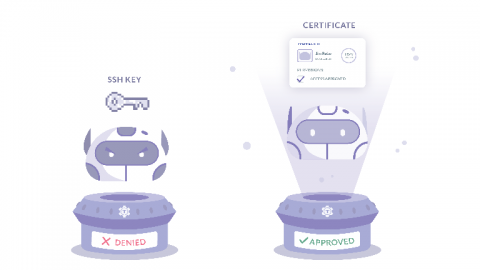
Applying the Principles of Zero Trust to SSH
The Zero Trust approach to security is based not on where you are, but who you are. This model shifts the focus from network and perimeter-based security to identity-based access. In simple terms, this means: Zero Trust security provides a powerful approach to keeping an organization’s resources secure and usage auditable.