Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Customize Your Automated Incident Severity Scoring Rules In GitGuardian
Shifting Left of Left: Secure Enterprise Data with JFrog Curation
In 2022, nearly 1,700 entities across the globe fell victim to software supply chain attacks, impacting over 10 million people. Nearly each of these attacks included some element of faulty or nefarious open-source code. Software developers commonly rely on open-source components to speed up the development process, but as we can see, this practice has the potential to introduce malicious packages and vulnerabilities into the code due to the lack of proper curation and maintenance.
How Software Supply Chain Attacks Work, and How to Assess Your Software Supply Chain Security
When it comes to applications and software, the key word is ‘more.’ Driven by the needs of a digital economy, businesses depend more and more on applications for everything from simplifying business operations to creating innovative new revenue opportunities. Cloud-native application development adds even more fuel to the fire. However, that word works both ways: Those applications are often more complex and use open-source code that contains more vulnerabilities than ever before.
Modern Strategies and Tools for Securing Internal Applications
Access for Hackers
Hello Teleport Community, Our team has just returned from Hacker Summer Camp (bSides Las Vegas, Blackhat and DEFCON). I met many customers, OSS users, hackers and security engineers at bSides. I had lots of great conversations at the bSides, and it was good to chat with both red and blue teams. This month’s newsletter is a review of some of my conversations from the week.
Submit Your Incident Feedback Directly In The GitGuardian Dashboard
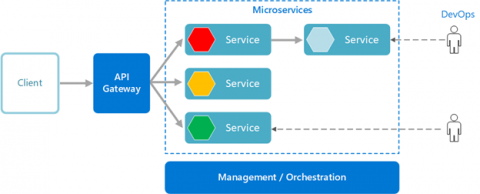
Seven DevSecOps Best Practices: Challenges and How to Address Them
DevSecOps best practices are increasingly being adopted to secure software supply chains. The challenge is finding ways to optimize these processes. Here are seven key considerations to help you adopt a successful and secure DevSecOps methodology.
Kubernetes 1.28: the security perspective
Teleport Achieves ISO 27001, HIPAA, and SOC 2 Compliance Milestones
We're thrilled to announce that Teleport has recently achieved critical compliance milestones, marking another significant step forward in our commitment to providing highly secure and reliable cloud-based services. We are pleased to inform you that Teleport has successfully achieved ISO 27001 certification, is now HIPAA compliant, and has also expanded our SOC 2 report coverage with the addition of Confidentiality and Availability trust service criteria.