Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
What Are the Most Common Security Risks of Cloud Computing?
Identifying and understanding the most common cloud security risks is crucial to a successful cloud computing adoption strategy. Organizations migrating to the cloud continually face new threats and discover vulnerabilities that were not present when they operated software deployed on-premises. According to IBM’s Cost of a Data Breach report, almost half of all data breaches are happening in the cloud, with attacks on systems hosted on public clouds costing an average of $5.02 million.
Real-time Security Alerts via Microsoft Teams
DevSecOps101: To Do or Not To Do
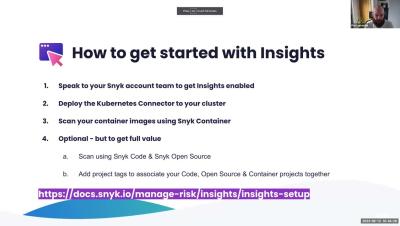
Office Hours: Insights - Focus on Top RIsks
Software Supply Chain Security: The Basics and Four Critical Best Practices
Modern enterprise software is typically composed of some custom code and an increasing amount of third-party components, both closed and open source. These third-party components themselves very often get some of their functionality from other third-party components. The totality of all of the vendors and repositories from which these components (and their dependencies) come make up a large part of the software supply chain.
Navigating Chaos: JFrog Security Essentials and Advanced Security
How to Achieve DevSecOps Success: Use Cases for the Financial Services Industry
How Software Supply Chain Security Regulation Will Develop, and What Will It Look Like?
The escalation of international legislative interest in regulating the software supply chain has led to an increasing likelihood that tools such as software bills of materials (SBOMs) and AppSec solutions will become essential for companies doing business in the public sector or in highly regulated industries. However, the process of building and enforcing effective regulations presents challenges as well.
How we built a secure RDP client
Today’s remote desktop protocol (RDP) clients don’t do enough to promote a strong security posture. They default to weak password-based authentication, leaving Windows infrastructure vulnerable to brute force attacks, and assume a direct connection to a well-known port is available. At Teleport we’re a bit bonkers about always trying to build the most secure solution, so we set out to do something different.