Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Technology
Securing Cloud Infrastructure with Teleport and AWS Identity Federation
Over the last decade, enterprises have accelerated the adoption of the cloud. According to the State of the Cloud report by Flexera, the average annual spend on cloud computing is over $62 million. As enterprises continue to invest in the cloud, AWS, the market leader in cloud computing, is growing at a rapid pace. The rise of cloud computing poses new challenges to enterprise IT. With each department migrating and managing their workloads in AWS, there is a proliferation of accounts, users and roles.
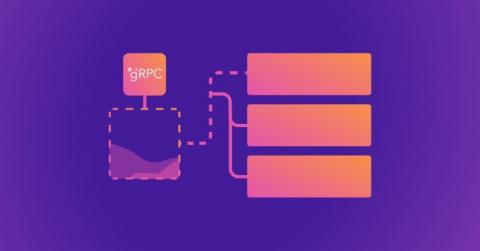
Building a secure API with gRPC
A Google remote procedure call (gRPC) is Google’s open source version of the remote procedure call (RPC) framework. It’s a communication protocol leveraging HTTP/2 and protocol buffer (protobuf) technologies. gRPC enables a remote client or server to communicate with another server by simply calling the receiving server’s function as if it were local. This makes communicating and transferring large data sets between client and server much easier in distributed systems.
What Does the Future of Password Security Look Like?
Passwords seem seriously inadequate for security in our lives. It seems they are always getting compromised or hacked through security flaws in apps, and they never seem strong enough. Most of us will be familiar with the headaches of finding the perfect 8-character-long password, only to be told that you’ve used that one before. Even though we know we should use a different password for every secure video conference or site we create accounts for, it’s hard to remember more than one!
Announcing: Code-free API log collection and parser creation
AT&T Cybersecurity is pleased to announce a code-free way for our USM Anywhere customers to make their own API-driven log collectors and custom parsers. This big advancement in threat detection and response technology will make it possible for customers to collect information from a much larger variety of sources and SaaS services without having to request new integrations or log parsers.
API authentication and authorization best practices
Comprehensive Risk-based API Protection
AWS RDS data security best practices
Amazon’s Relational Database Service (AWS RDS) allows you to offload the responsibility of managing a database, but it also comes with the risk of another external dependency. Fortunately, AWS provides some tools and settings to help with this. When you combine your existing data security policy with the AWS tooling and the advice in this article, you'll be well on your way to managing risk more effectively. Let's dive in with 15 AWS RDS data security best practices.
Financial Services Software Has Fewer Security Flaws Than Most Industries
Establishing a mobile device vulnerability management program
The introduction of mobile devices has rapidly changed the world as we know it, as these small gadgets that are intended to fit into the palm of our hands rapidly gained dominance over our day-to-day activities. Thanks to these portable devices, we now have access to an abundance of information available to us on demand with minimal effort.