Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
%term
Low-Code for Dummies - An Overview of Low-Code Through Examples
While the mission statement of the Zenity Low-Code Security Blog is to help organizations adopt low-code platforms securely and with confidence, we often find ourselves explaining basic low-code concepts and principles - mostly to those who are not familiar with the day-to-day low-code development process.
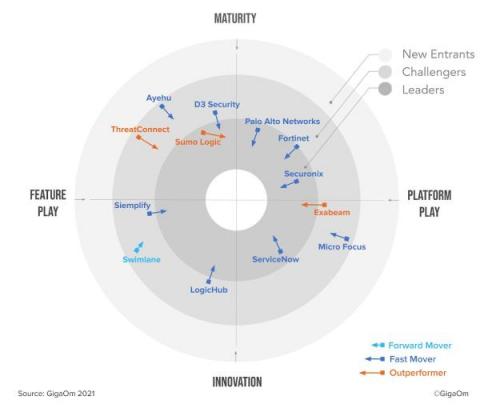
Sumo Logic recognized as a Leader in the GigaOm Radar Report for Security Orchestration, Automation, and Response (SOAR)
Introducing the Security Visionaries Podcast
I am often asked what has changed and what will need to change most about cybersecurity in the next few years, especially as we come out the other side of a global pandemic that upended all kinds of plans. But let’s start by level-setting: the grand strategy for security—protect data—hasn’t changed. It’s the tactics that have changed, and more importantly, must continue to change.
Cloud Threats Memo: Manage Your Leaky Public Cloud Misconfigurations
A new day, a new wave of S3 leaks… Cloud misconfigurations continue to be a major concern for organizations and a constant source of data leaks. A recent report by IBM has revealed that misconfigurations are behind two-thirds of cloud security incidents.
Splunk SOAR Feature Overview: Apps
Splunk SOAR Feature Overview: App Editor
IT/OT Convergence: How IT and OT Can Work Together to Limit Production Risk
What Pandemic Responses Teach Us About Cybersecurity
I’ve been working at Tripwire for over two decades, and I’ve acquired a fair bit of swag over those years: branded jackets, hats, shoes, a watch, and of course a drawer full of t-shirts. One thing I never would have predicted owning was a Tripwire-branded face mask to protect me from a global pandemic. Over the past year, I’ve worn that face mask more than any of my other swag. Of course, none of my other swag protected me and others from a highly contagious, deadly virus.
How does encryption remove risk for auditors?
For those in the security space or at C-level, you’ve likely seen a recommendation about how to manage encryption and corresponding keys. Or at least something about encryption needing further consideration. Chances are, if you’re reading this you have at least an interest in the topic and are researching relevant products.