TicketMaster breach: Leaked credentials are the golden ticket once again
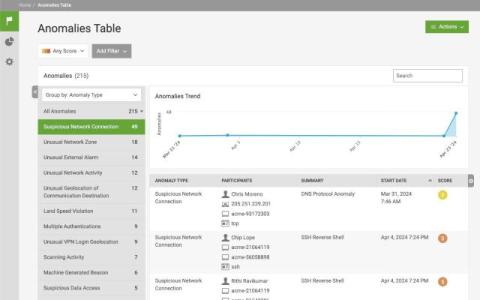
It had already been a challenging few weeks for Live Nation Entertainment, Inc. as they faced down a lawsuit from The Justice Department regarding anti-competitive practices. Things got worse at the end of May when a cybercriminal known as “SpidermanData” claimed to have breached a huge database of 560 million records (including personal and financial data) belonging to TicketMaster Entertainment, LLC – a Live Nation company.