Black Hat NOC: Zero Trust...but Verify | Corelight
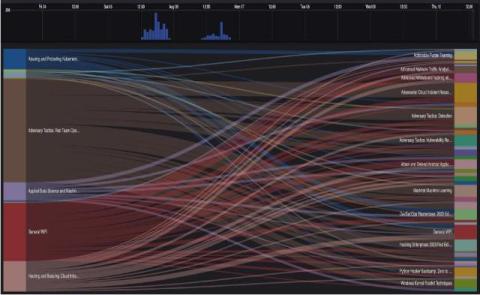
The Black Hat network is unlike an enterprise network. The network operations center (NOC), which Corelight helps to operate, sees traffic that would never be permissible on most enterprise networks. Still, in many ways the Black Hat network is a microcosm of many real-world environments, with similar challenges that require similar solutions.