Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
JFrog
JFrog Log Analytics with Datadog just got better!
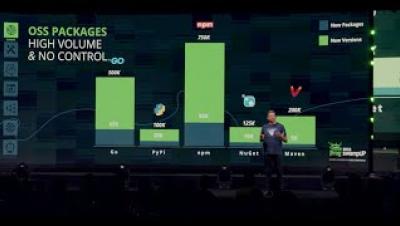
The software supply chain today runs differently than it did just five years ago. The number of available tools, languages, and packages used have exploded. Further, the growing mix of OSS packages puts organizations at risk of outdated software, untracked dependencies, and non-compliant licenses. To add to the chaos, teams are now increasingly distributed and greater in number. All of this dramatically increases the number of inputs within the software supply chain.
Rising CVEs and the need for speed: Enhancing software security with JFrog Xray and PagerDuty
With the proliferation of CVEs (Common Vulnerabilities and Exposures), we have witnessed a remarkable surge in associated risks over the past five years. 2022 was a record-breaking year with 25,096 new CVEs found, the most discovered CVEs ever. Unfortunately, 2023 is on track to beat that record.
CSO View on Software Supply Chain Security
Cloud Integrations: JFrog Achieves AWS PrivateLink Service Ready Validation
At JFrog, we talk about being universal and too integrated to fail. In addition to more than 30 technologies and package types supported natively, this also means supporting our customers in their hybrid and cloud infrastructure. One such key integration capability for customers leveraging Amazon Web Services (AWS) is AWS PrivateLink.
DevNext Workshop 2: Innovate More...Remediate Less with JFrog DevOps-Centric Security
Release Fast and Secure or Die!
Shielding the Foundation: Security Across Your SSC
International Cyber Security Month Tips
Securing your software supply chain is crucial for ensuring the integrity and security of the software you develop and deliver. Here are the top 8 security best practices for a secure software supply chain.
Arbitrary File Creation vulnerability in plexus-archiver - CVE-2023-37460
The JFrog Security research team constantly monitors open-source projects to find new vulnerabilities or malicious packages and share them with the wider community to help improve their overall security posture. As part of this effort, the team recently discovered a new security vulnerability in plexus-archiver, an archive creation and extraction package.