Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Supply Chain
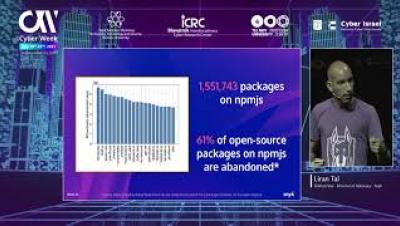
Are We Forever Doomed By Software Supply Chain Risks? Cyber Week Israel 2021, Liran Tal
How to Secure Your Supply Chain
How Network Segmentation Can Protect Supply Chains from Ransomware Attacks
Organizations can take various steps to protect their operational technology (OT) environments against digital threats. But some stand out more than others. In particular, network segmentation is described as “the first answer to insufficient ICS (Industrial Control System) cybersecurity.” Experts advocate zoning ICS assets to coordinate informational technology (IT) and OT environments effectively. That doesn’t always happen, however.
Last (Executive) Orders Please: Supply Chains, Policy and Modernising Cybersecurity
An EO is a written, signed, and published directive from the President that manages operations of the federal government, and although some EO’s require legislative approval, they effectively become law. It comes on the back of several high profile incidents involving Microsoft (Exchange), SolarWinds and the recent Colonial Pipeline incident. It is seen as a much-needed step to modernise and protect federal networks and improve information sharing between the private and US government.
How Packages' External Resources Threaten Your Supply Chain
Many developers already know that in some ecosystems, open source dependencies might run their custom code from packages when they are being installed. While this capability can be used for both good and evil, today we’ll focus on a legit use case that, when misused, can escalate and be used to compromise your organization’s supply chain. If you haven’t guessed yet, I’m talking about downloading and linking external dependencies during the install process.
Protect Your Retail Supply Chain Against Cyber Attacks
Protecting the Supply Chain in COVID-19
Reduce open source software risks in your supply chain
Knowing what’s in your open source software, whether you’re a consumer or producer, can help you manage security risks in your supply chain Modern open source software (OSS) is a movement that started in the eighties as a reaction to commercial software becoming more closed and protected. It allowed academics, researchers, and hobbyists to access source code that they could reuse, modify, and distribute openly.
Why the Biggest Threat Facing Supply Chains is on the Inside
Businesses need to act now to survey their supply chain, developing the capacity to anticipate and respond to supply chain risks, minimizing the impact and optimizing opportunity. In March, the world witnessed a curious scene. A container ship longer than the Empire State Building became lodged in Egypt’s Suez Canal, creating an incredible spectacle as heavy construction equipment and a fleet of tug boats tried to dislodge the vessel from the canal walls.