Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Supply Chain
Supply Chain Security Update: How Secure is Composer?
When it comes to PHP, composer is without discussion, THE package manager. It’s fast, easy to use, actively maintained and very secure — or so most thought. On April 21, 2021, a command injection vulnerability was reported, which shook the PHP community. Fortunately it didn’t have a very big impact, but it could have. The problem with the vulnerability is that it affected the very heart of the Composer supply chain: Packagist servers.
Detect and prevent dependency confusion attacks on npm to maintain supply chain security
On February 9, 2021, Alex Birsan disclosed his aptly named security research, dependency confusion. In his disclosure, he describes how a novel supply chain attack that exploits misconfiguration by developers, as well as design flaws of numerous package managers in the open source language-based software ecosystems, allowed him to gain access and exfiltrate data from companies such as Yelp, Tesla, Apple, Microsoft, and others.
Anatomy of a Supply Chain Attack: How to Accelerate Incident Response and Threat Hunting
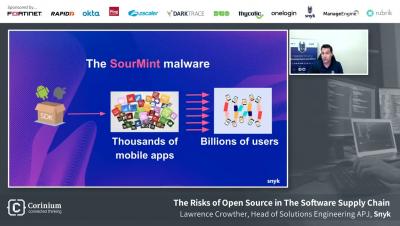
In recent months, we’ve seen a sharp rise in software supply chain attacks that infect legitimate applications to distribute malware to users. SolarWinds, Codecov and Kesaya have all been victims of such attacks that went on to impact thousands of downstream businesses around the globe. Within minutes of these high-profile attacks making headline news, CEOs often ask: “Should we be concerned? How is it impacting us? What can we do to mitigate risk?” .
What is the Digital Supply Chain?
The supply chain for any product has several moving parts. Each activity in the supply chain plays a role in the flow that begins with sourcing a product's raw materials and ends with delivering the finished goods to a customer. As with many other areas of modern business, digital technologies are redefining supply chains. With more technology comes increased cyber risks. This article explains digital supply chains along with their benefits and cybersecurity risks.
Ransom Attacks & Supply Chains :The Soft Underbelly of Secure Enterprise Systems
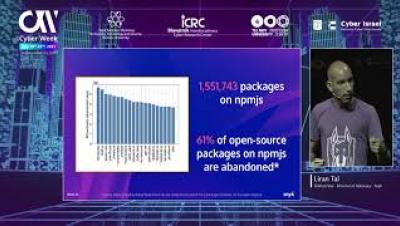
Are We Forever Doomed By Software Supply Chain Risks? Cyber Week Israel 2021, Liran Tal
How to Secure Your Supply Chain
How Network Segmentation Can Protect Supply Chains from Ransomware Attacks
Organizations can take various steps to protect their operational technology (OT) environments against digital threats. But some stand out more than others. In particular, network segmentation is described as “the first answer to insufficient ICS (Industrial Control System) cybersecurity.” Experts advocate zoning ICS assets to coordinate informational technology (IT) and OT environments effectively. That doesn’t always happen, however.