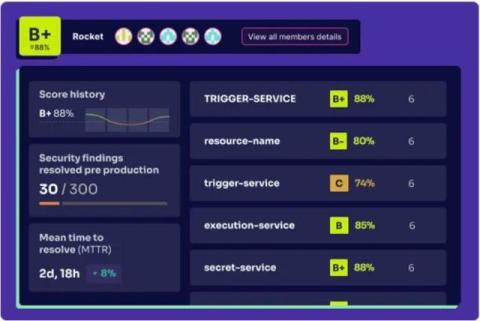
Financial Services Industry Experiences a Massive Increase in Brand Abuse
Industry analysis of the domains used behind phishing and brand impersonation attacks show financial institutions are being leveraged at an alarming rate. It’s one thing to see your industry at the top of some “state of” cybersecurity report, but it’s entirely different to learn that 68% of all phishing web pages identified in a single quarter are from your industry. That’s exactly what we find in Akamai’s latest analysis of websites across the Internet.