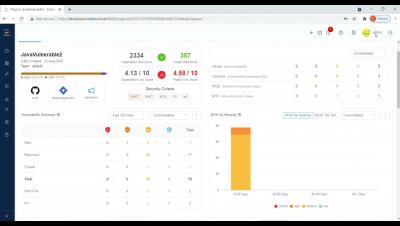
5 Tips to Provide Your Customers with The Advanced Endpoint Security They Really Need
Advanced cybersecurity is now the baseline of complex IT environments that include computers, servers, laptops, and other devices that may be used within the corporate network but also outside the office. It is also critical to face the growing threat landscape of advanced, silent, and targeted attacks. But how can you make sure you meet each of your customers’ specific requirements and deliver a cutting-edge IT approach in a way that is sustainable for your business?