Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
%term
Red Teaming: How to Run Effective Cyber-Drills?
What is red teaming? How is it different from conventional penetration testing? Why do we need blue, red, and white teams? How are cyber-drills carried out, and what results should be expected? In this article, we will answer these and other questions related to red teaming.
Business Continuity With Egnyte For Those Impacted by Coronavirus
The COVID-19 virus (or coronavirus) is having an impact on businesses across the globe. Organizations have been pressed to balance productivity with the protection of their employees and partners. With that in mind, we’ve collected a few helpful resources from Egnyte that can help enable continuity in times of business disruption.
What is really an API?
API has become one of those catch-all terms that developers throw around without really considering the context. On any given week, you will come across discussions like "How to use the Twitter API", "New framework X is great because it has a low API surface", and "Best practices for building an API." Is an API a data source? Is it a service? Is it a way to call native functionality? The truth is, in modern software development it can mean any of these things.
Inherent Risk vs. Control Risk: What's the Difference?
Inherent risk and control risk are two of the three parts of the audit risk model, which auditors use to determine the overall risk of an audit. Inherent risk is the risk of a material misstatement in a company’s financial statements without considering internal controls.
Gehaxelt - How Wordpress Plugins Leak Sensitive Information Without You Noticing
Sebastian Neef (@gehaxelt) is a IT security freelancer and a top contributor from the Detectify Crowdsource community. In this guest blog, he looks at ways WordPress plugins leak sensitive data in the wild: The OWASP Top 10 puts Sensitive Data Exposure on the 3rd place of the most common web security issues. In this blog post we will have a look at sensitive data exposure that you might not be aware of.
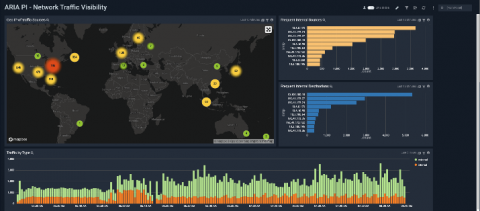
A New Integration between Sumo Logic and ARIA Cybersecurity Solutions
NSA Releases Cloud Vulnerability Guidance
The United States’ National Security Agency (NSA) has put together a short guidance document on mitigating vulnerabilities for cloud computing. At only eight pages, it is an accessible primer for cloud security and a great place to start before taking on something like the comprehensive NIST 800-53 security controls.
The advantages of resource-based pricing in security
Given the complexity of large enterprise environments, coupled with the diversity of the vendor landscape, there is no single, agreed-upon “best” way to buy security. The battles continue between CAPEX or OPEX, net-30 or net-90, annual or multi-year, perpetual or subscription. One thing we do know, however, is that all too often the consumer pays for something he or she does not use.
What is a Data Breach and How It Can Be Cured? (Part 1)
In the age of the digital world, cyber threats and vulnerabilities have gained the attention of security leaders as well as countries across the globe. The issue of cyber warfare is no longer limited to organizations. Rather, even state-sponsored cyber-attacks are being organized and launched against enemy states.