Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
SOAR
The latest News and Information on Security Orchestration, Automation and Response.
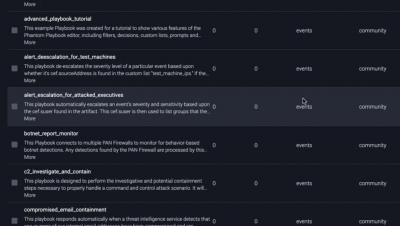
Splunk SOAR Feature Video: Playbooks
Orchestrate Framework Controls to Support Security Operations with Splunk SOAR
Every security team should utilize security frameworks in their strategy and tactics to help reduce risk from common cybersecurity threats. Security frameworks guide organizations on how they should develop, build, and maintain their IT security policies and procedures while sharing best practices for meeting compliance requirements. Healthcare operations in particular are often presented with increasing regulatory scrutiny and obligations that must be met in order to be competitive.
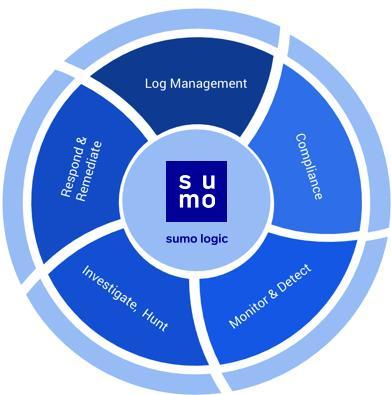
Sumo Logic to accelerate modernization of security operations with proposed acquisition of DFLabs
Splunk for OT Security V2: SOAR and More
In the last 90 days, the news of cyberattacks on critical infrastructure has been stunning. From the unprecedented breach represented by Sunburst to the more recent bone-chilling attack at the Oldsmar water facility, the urgency to secure critical infrastructure in transportation, utilities, energy, water, critical manufacturing, telecommunications, healthcare, government facilities and the defense sector has never been higher.
Splunk SOAR Playbooks: Crowdstrike Malware Triage
Automating With Splunk Phantom: How Norlys Does It
Some tasks are better off automated. Paying bills on time? Automated payments. Orchestrating a coordinated response to security alerts and triaging security events? There’s Splunk Phantom for that. Monotonous tasks, in our work and personal lives, should and can be automated in order to free up time and energy to focus on the things that matter.
A Path to Proactive Security Through Automation
The sheer number of cyberattacks launched against organizations every year is massive and growing. If you’re a security analyst working in a SOC or security team, tasked with defending your organization, that means you’re getting bombarded by many more attacks than the recorded numbers above would suggest. These attacks translate into security alerts — fired from your various security tools — that you must investigate and resolve.
Next Level Automation: What's New with Splunk Phantom
Splunk Phantom 4.10 introduced many new enhancements, including the ability to develop playbooks in Python 3. In fact, Python 3 is now the default for Splunk Phantom playbooks. In doing so, we needed to create two different “playbook runners” to ensure we could continue to support playbooks written in Python 2.7 while also supporting Python 3.
Splunk SOAR Playbooks: Finding and Disabling Inactive Users on AWS
Every organization that uses AWS has a set of user accounts that grant access to resources and data. The Identity and Access Management (IAM) service is the part of AWS that keeps track of all the users, groups, roles and policies that provide that access. Because it controls permissions for all other services, IAM is probably the single most important service in AWS to focus on from a security perspective.